Common Vulnerabilities and Exposures (CVE)number
CVE-2010-2883 Stack-based buffer overflow in CoolType.dll in Adobe Reader and Acrobat 9.x before 9.4, and 8.x before 8.2.5 on Windows and Mac OS X, allows remote attackers to execute arbitrary code or cause a denial of service (application crash) via a PDF document with a long field in a Smart INdependent Glyphlets (SING) table in a TTF font, as exploited in the wild in September 2010. NOTE: some of these details are obtained from third party information
General File Information
File invitation.pdf
MD5 : 29db2fba7975a16dbc4f3c9606432ab2
SHA1 : 5d65e6984e521936707b32219b39388efb4296fa
File size :344218 bytes
Type: PDF
Distribution: Email attachment
Post Updates
Nov 8, 2010 Post by Mikko H. Hyppönen on F-Secure blog - Case Nobel
- Nov 10, 2010 CPJ. Committee to Protect Journalists. That Nobel invite? Mr. Malware sent it -- By Danny O'Brien/CPJ Internet Advocacy Coordinator
- Nov 10, 2010 Computerworld (Norway) New attack against Nobel Prize by Ole Petter Baugerød Stokke (Google Translated)
- Nov 10, 2010 Le Figaro*fr Nobel: new computer attack (Google translated)
- Nov 10, 2010 APF Google New cyber attack linked to Nobel Peace Prize
- Nov. 13 Infowar Monitor Nobel Peace Prize, Amnesty HK and Malware by Nart
More about similar attacks
- Oct 22, 2010 Infowar Monitor Command and Control in the Cloud
- Aug 19, 2010 Infowar Monitor Human Rights and Malware Attacks
Download
Original Message
[mailto:alexXXX@XXXforum.com]
Sent: Sunday, November 07, 2010 7:34 PM
To: XXXXXXXXXX
Subject: An invitation to the Nobel Prize ceremony of Liu Xiaobo
Dear Sir / Madame
I enclose a letter from Oslo Freedom Forum founder Thor Halvorssen inviting
you to join him in Oslo for the Dec. 11th Prize ceremony. Let me know if you
have any questions.
Sincerely yours,
Alex XXXXX
--
Vice President of Strategy
Oslo Freedom Forum
alexXXXXX@XXXXXforum.com
Message Headers
Received: (qmail 18379 invoked from network); 8 Nov 2010 00:36:59 -0000Received: from capricorn.priced2go.net (HELO capricorn.priced2go.net) (97.65.113.26)
by XXXXXXX; 8 Nov 2010 00:36:59 -0000
Received: from mailserver.com ([96.56.210.156]) by capricorn.priced2go.net with Microsoft SMTPSVC(6.0.3790.4675);
Sun, 7 Nov 2010 16:36:23 -0800
Reply-To: "Alex XXXXX"
From: "Alex XXXXX"
To: XXXXX
Subject: An invitation to the Nobel Prize ceremony of Liu Xiaobo
Date: Mon, 8 Nov 2010 08:34:15 +0800
MIME-Version: 1.0
Content-Type: multipart/mixed; boundary="DTOEUDDBGIE"
X-Priority: 3
X-MSMail-Priority: Normal
Return-Path: alexXXXXX@XXXXXXforum.com
Message-ID:
X-OriginalArrivalTime: 08 Nov 2010 00:36:24.0028 (UTC) FILETIME=[F8AE79C0:01CB7EDC]
Sender
mirage_2008@hotmail.comHostname: ool-6038d20f.static.optonline.net
ISP: Optimum Online
Organization: MARK WIESEN MD
Country: United States
State/Region: New Jersey
Automated Scans
File name:invitation.pdfhttp://www.virustotal.com/file-scan/report.html?id=e134afd2ac6d04f37da7ccdf54ba298cc439a02c56636a855a8d51ee025fb697-1289198253
Submission date:2010-11-08 06:37:33 (UTC)
Current status:queued (#18) queued (#19) analysing finished
Result:21/ 43 (48.8%)
AntiVir 7.10.13.164 2010.11.07 HTML/Shellcode.Gen
Avast 4.8.1351.0 2010.11.07 PDF:CVE-2010-2883
Avast5 5.0.594.0 2010.11.07 PDF:CVE-2010-2883
AVG 9.0.0.851 2010.11.07 Exploit_c.KAH
BitDefender 7.2 2010.11.08 Exploit.PDF-TTF.Gen
DrWeb 5.0.2.03300 2010.11.08 Exploit.PDF.1608
eTrust-Vet 36.1.7958 2010.11.05 PDF/CVE-2010-2883.A!exploit
F-Secure 9.0.16160.0 2010.11.08 Exploit.PDF-TTF.Gen
Fortinet 4.2.249.0 2010.11.07 PDF/CoolType!exploit.CVE20102883
GData 21 2010.11.08 Exploit.PDF-TTF.Gen
Kaspersky 7.0.0.125 2010.11.08 Exploit.Win32.CVE-2010-2883.a
McAfee-GW-Edition 2010.1C 2010.11.07 Heuristic.BehavesLike.PDF.Suspicious.O
Microsoft 1.6301 2010.11.08 Exploit:Win32/ShellCode.A
NOD32 5599 2010.11.07 PDF/Exploit.Gen
Norman 6.06.10 2010.11.07 PDF/Suspicious.D
nProtect 2010-11-08.01 2010.11.08 Exploit.PDF-Name.Gen
PCTools 7.0.3.5 2010.11.08 HeurEngine.MaliciousExploit
Sophos 4.59.0 2010.11.08 Troj/PDFEx-DW
Symantec 20101.2.0.161 2010.11.08 Bloodhound.Exploit.357
TrendMicro 9.120.0.1004 2010.11.08 TROJ_PIDIEF.SMZA
TrendMicro-HouseCall 9.120.0.1004 2010.11.08 TROJ_PIDIEF.SMZA
MD5 : 29db2fba7975a16dbc4f3c9606432ab2
SHA1 : 5d65e6984e521936707b32219b39388efb4296fa
Analysis / CVE ID
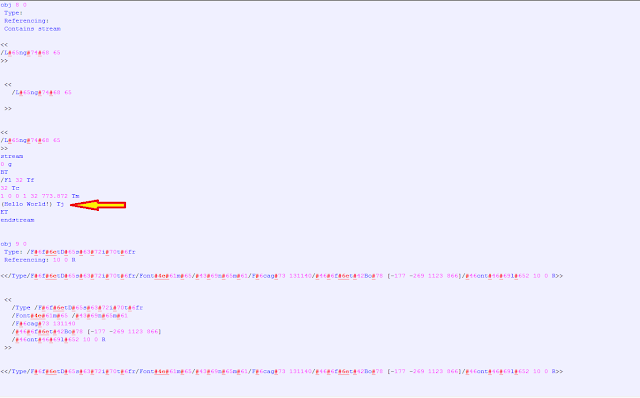
Metasploit generated CVE-2010-2883Exploit PDF
Files Created
%Temp%\invitation.pdf
File: invitation.pdf
Size: 242200
MD5: 4BC0F7B7A4804C40AF1EB131EAE51102
%Temp%\svchost.exe
http://www.virustotal.com/file-scan/report.html?id=b98740ac6814d0228d7af41adebe54a9086a65f9ddcbb79d008bc72e5146f50b-1289199948
File: svchost.exe
Size: 57344
MD5: 5336A443D420A80F6FB4A39672E82804
File name: svchost.exe
Submission date: 2010-11-08 07:05:48 (UTC)
Result: 11/ 42 (26.2%)
Antiy-AVL 2.0.3.7 2010.11.08 Trojan/Win32.OnLineGames.gen
Avast 4.8.1351.0 2010.11.07 Win32:Malware-gen
Avast5 5.0.594.0 2010.11.07 Win32:Malware-gen
ClamAV 0.96.2.0-git 2010.11.08 Trojan.Spy-77644
F-Prot 4.6.2.117 2010.11.07 W32/Dorando.B.gen!Eldorado
F-Secure 9.0.16160.0 2010.11.08 Trojan.Generic.4974556
GData 21 2010.11.08 Win32:Malware-gen
NOD32 5599 2010.11.07 Win32/Agent.RZF
nProtect 2010-11-08.02 2010.11.08 Trojan-PWS/W32.WebGame.57344.EP
TheHacker 6.7.0.1.080 2010.11.08 Trojan/Agent.rzf
VBA32 3.12.14.1 2010.11.05 TrojanPSW.OnLineGames.xevz
MD5 : 5336a443d420a80f6fb4a39672e82804
Network activity
phile.3322.org 117.65.58.237
Update Nov 10, 2010 -- IP address of the server is now 117.65.58.36
Hostname: 117.65.58.237
ISP: CHINANET Anhui province network
Organization: CHINANET Anhui province network
Type: Broadband
Assignment: Static IP
Country: China
State/Region: Anhui
City: Bengbu
Download pcap file for 117.65.58.237
Download pcap file for 117.65.58.36











No comments:
Post a Comment