Common Vulnerabilities and Exposures (CVE)number
CVE-2010-3654 Adobe Flash Player 10.1.85.3 and earlier on Windows, Mac OS X, Linux, and Solaris and 10.1.95.2 and earlier on Android, and authplay.dll (aka AuthPlayLib.bundle or libauthplay.so.0.0.0) in Adobe Reader and Acrobat 9.x through 9.4, allows remote attackers to execute arbitrary code or cause a denial of service (memory corruption and application crash) via crafted SWF content, as exploited in the wild in October 2010.
General File Information
File Name: News Release.pdf
MD5 411406d5ace2201e5dd73ce8e696b03b
SHA1 : 92e03aa29715951061d8dd17ea59221fc8ea1d65
File size : 241679 bytes
Type: PDF
Distribution: Email attachment
Download
 Download News Release.pdf as a password protected archive (contact me if you need the password)
Download News Release.pdf as a password protected archive (contact me if you need the password)Download dropped files listed below as a password protected archive (contact me if you need the password)
If you need a sample for developing protection for your customers/users or testing security products, email me.
Please note that the malicious PDF itself will NOT be publicly released on Contagio until Adobe
issues a security update / patch for Flash player (expectedNovember 9, November 5, 2010)
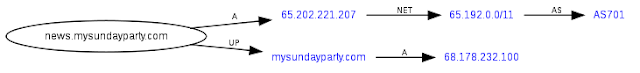
Update 5. Nov 4, 2010 The IP of news.mysundayparty.com is changing
Original was 65.202.221.207, then it changed to 63.232.79.43, today it is 65.202.221.207 again
news.mysundayparty.com. A 65.202.221.207
first seen 2010-10-28 23:58:14 -0000
last seen 2010-10-29 06:37:15 -0000
news.mysundayparty.com. A 63.232.79.43
first seen 2010-10-29 19:47:29 -0000
last seen 2010-10-30 13:10:27 -0000
Update 4. Oct 28, 2010 11:40 pm
issues a security update / patch for Flash player (expected
Update 5. Nov 4, 2010 The IP of news.mysundayparty.com is changing
Original was 65.202.221.207, then it changed to 63.232.79.43, today it is 65.202.221.207 again
news.mysundayparty.com. A 65.202.221.207
first seen 2010-10-28 23:58:14 -0000
last seen 2010-10-29 06:37:15 -0000
news.mysundayparty.com. A 63.232.79.43
first seen 2010-10-29 19:47:29 -0000
last seen 2010-10-30 13:10:27 -0000
Update 4. Oct 28, 2010 11:40 pm
Please scroll down to see information about the PDF file, dropped/created files and associated traffic
Update 3. Oct 28, 2010 10:07 pm
A very good analysis has been published by Villy at New Adobe 0day (bug in flash player) http://bugix-security.blogspot.com
 Adobe issued a bulletin CVE-2010-3654 Security Advisory for Adobe Flash Player, Adobe Reader and Acrobat
Adobe issued a bulletin CVE-2010-3654 Security Advisory for Adobe Flash Player, Adobe Reader and Acrobat A Security Advisory (APSA10-05) has been posted in regards to a new Flash Player, Adobe Reader and Acrobat issue (CVE-2010-3654). A critical vulnerability exists in Adobe Flash Player 10.1.85.3 and earlier versions for Windows, Macintosh, Linux and Solaris operating systems; Adobe Flash Player 10.1.95.2 and earlier versions for Android; and the authplay.dll component that ships with Adobe Reader 9.4 and earlier 9.x versions for Windows, Macintosh and UNIX operating systems, and Adobe Acrobat 9.4 and earlier 9.x versions for Windows and Macintosh operating systems. This vulnerability (CVE-2010-3654) could cause a crash and potentially allow an attacker to take control of the affected system. There are reports that this vulnerability is being actively exploited in the wild against Adobe Reader and Acrobat 9.x. Adobe is not currently aware of attacks targeting Adobe Flash Player
Update 1. Oct 28, 2010 6:10 am
Tom Ferris has confirmed it as well:
tferris Based on the PoC that @snowfl0w sent me, a Flashplayer 0day seems to be making it rounds.. Adobe PSIRT has been notified
Heh, here is a small article about this finding in the news already this morning.. Unpatched Critical Flash Player Vulnerability Possibly Exploited in the Wild by Lucian Constantin from http://news.softpedia.com/
Adobe was notified. The bug has not been confirmed by Adobe yet. Once we get a confirmation or correction, we will post it as well.
Original Message
Automated Scans
File name: CVE-2010-3654_pdf_2010-10-26_News Release.pdfSubmission date:2010-10-29 02:11:21 (UTC)
http://www.virustotal.com/file-scan/report.html?id=ed3503c107826bc256208a49f59a4faf2e226c94000853bef00f15fef02f73dc-1288318281
 14/ 42 (33.3%)
14/ 42 (33.3%)Avast 4.8.1351.0 2010.10.29 JS:Pdfka-gen
Avast5 5.0.594.0 2010.10.29 JS:Pdfka-gen
AVG 9.0.0.851 2010.10.28 Exploit_c.NLK
BitDefender 7.2 2010.10.29 Exploit.PDF-JS.Gen
Emsisoft 5.0.0.50 2010.10.29 Virus.JS.Pdfka!IK
F-Prot 4.6.2.117 2010.10.28 W32/Heuristic-XEN!Eldorado
F-Secure 9.0.16160.0 2010.10.29 Exploit:W32/Pidief.CSR
GData 21 2010.10.29 Exploit.PDF-JS.Gen
Ikarus T3.1.1.90.0 2010.10.29 Virus.JS.Pdfka
McAfee-GW-Edition 2010.1C 2010.10.28 Heuristic.BehavesLike.PDF.Suspicious.O
 Microsoft 1.6301 2010.10.28 Exploit:Win32/Pdfjsc.gen!A
Microsoft 1.6301 2010.10.28 Exploit:Win32/Pdfjsc.gen!AnProtect 2010-10-28.01 2010.10.28 Exploit.PDF-JS.Gen
Panda 10.0.2.7 2010.10.29 Exploit/PDF.Flash.A
Symantec 20101.2.0.161 2010.10.29 Trojan.Pidief
Additional information
Show all
MD5 : 411406d5ace2201e5dd73ce8e696b03b
Analysis
- New Adobe 0day (bug in flash player) http://bugix-security.blogspot.com by Villy777
- Fuzz My Life: Flash Player zero-day vulnerability (CVE-2010-3654) Fortinet
Files Created

%TEMP%
File: ~temp.batSize: 132
MD5: 8B7A45A9494D047896DFFB813D7DEB35
ping 127.0.0.1 -n 3 & taskkill /im Acrobat.exe /f & taskkill /im AcroRd32.exe /f & "C:\DOCUME~1\Mila\LOCALS~1\Temp\News Release.pdf"
----------------------------------------------------------------------------------- File: News Release.pdf
Size: 16527
MD5: B0ABDF5E37ED82A334D7422CDD68DE4F
-----------------------------------------------------------------------------------
File: nsunday.dll
Size: 27649
MD5: 31E0D52EDCF2BBE8A05849D357A03302
File name:nsunday.dll
http://www.virustotal.com/file-scan/report.html?id=8b088f16c39972e7a5f57d9ca13d78c186e4ecd7b17bbefc868107399fba1f74-1288321831
Submission date:2010-10-29 03:10:31 (UTC)
Result:23/ 42 (54.8%)
AhnLab-V3 2010.10.29.00 2010.10.28 Win-Trojan/Wisp.27649
AntiVir 7.10.13.67 2010.10.28 HEUR/Malware
Avast 4.8.1351.0 2010.10.29 Win32:Malware-gen
Avast5 5.0.594.0 2010.10.29 Win32:Malware-gen
AVG 9.0.0.851 2010.10.28 Generic19.BYBD
BitDefender 7.2 2010.10.29 Backdoor.Generic.497009
Comodo 6546 2010.10.29 UnclassifiedMalware
DrWeb 5.0.2.03300 2010.10.29 BackDoor.Terapy.1
F-Secure 9.0.16160.0 2010.10.29 Backdoor.Generic.497009
GData 21 2010.10.29 Backdoor.Generic.497009
Ikarus T3.1.1.90.0 2010.10.29 Trojan.Win32.Wisp
McAfee 5.400.0.1158 2010.10.29 Generic.dx!ule
McAfee-GW-Edition 2010.1C 2010.10.28 Generic.dx!ule
Microsoft 1.6301 2010.10.28 Trojan:Win32/Wisp.gen!A
NOD32 5573 2010.10.29 a variant of Win32/Wisp.B
nProtect 2010-10-28.01 2010.10.28 Backdoor.Generic.497009
Panda 10.0.2.7 2010.10.29 Suspicious file
PCTools 7.0.3.5 2010.10.29 Backdoor.Trojan
Prevx 3.0 2010.10.29 Medium Risk Malware
Sophos 4.59.0 2010.10.29 Troj/Wisp-A
Sunbelt 7161 2010.10.29 Trojan.Win32.Generic!BT
SUPERAntiSpyware 4.40.0.1006 2010.10.29 -
Symantec 20101.2.0.161 2010.10.29 Backdoor.Trojan
VBA32 3.12.14.1 2010.10.28 BackDoor.Terapy.1
Additional information
Show all
MD5 : 31e0d52edcf2bbe8a05849d357a03302
--------------------------------------------------------------------------------------------
File: nsunday.exe
Size: 153600
MD5: 20F8B25A9A57B07895E112DAECB1C4CC
File name:nsunday.exe
http://www.virustotal.com/file-scan/report.html?id=beec0289bcd9625a6498b4cc93ed691148b17e6a13460b7af3825f6e5dd74d2a-1288322070
Submission date:2010-10-29 03:14:30 (UTC)
24/ 41 (58.5%)
AhnLab-V3 2010.10.29.00 2010.10.28 Win-Trojan/Wisp.153600
AntiVir 7.10.13.67 2010.10.28 TR/Dropper.Gen
Antiy-AVL 2.0.3.7 2010.10.29 Trojan/Win32.heuristic
Avast 4.8.1351.0 2010.10.29 Win32:Malware-gen
Avast5 5.0.594.0 2010.10.29 Win32:Malware-gen
AVG 9.0.0.851 2010.10.28 Dropper.Generic2.BNQT
BitDefender 7.2 2010.10.29 Gen:Trojan.Heur.RP.jqZ@aeVV!!ab
Comodo 6546 2010.10.29 UnclassifiedMalware
DrWeb 5.0.2.03300 2010.10.29 Trojan.MulDrop1.46814
eSafe 7.0.17.0 2010.10.28 Win32.TRDropper
F-Secure 9.0.16160.0 2010.10.29 Gen:Trojan.Heur.RP.jqZ@aeVV!!ab
GData 21 2010.10.29 Gen:Trojan.Heur.RP.jqZ@aeVV!!ab
Jiangmin 13.0.900 2010.10.28 Trojan/Scar.cyn
McAfee 5.400.0.1158 2010.10.29 Generic.dx!ule
McAfee-GW-Edition 2010.1C 2010.10.28 Heuristic.BehavesLike.Win32.PasswordStealer.H
Microsoft 1.6301 2010.10.28 Trojan:Win32/Wisp.gen!A
NOD32 5573 2010.10.29 probably a variant of Win32/Wisp.A
Panda 10.0.2.7 2010.10.29 Suspicious file
PCTools 7.0.3.5 2010.10.29 Backdoor.Trojan
Prevx 3.0 2010.10.29 Medium Risk Malware Dropper
Sophos 4.59.0 2010.10.29 Mal/Dropper-P
Sunbelt 7161 2010.10.29 BehavesLike.Win32.Malware.tsc (mx-v)
Symantec 20101.2.0.161 2010.10.29 Backdoor.Trojan
VBA32 3.12.14.1 2010.10.28 Trojan.Win32.Inject.2
MD5 : 20f8b25a9a57b07895e112daecb1c4cc
File: nsunday.exe
MD5: 20f8b25a9a57b07895e112daecb1c4cc
Size: 153600
Ascii Strings:
HTTP/1.0-----------------------------------------------------------------------------------
http://www.yahoo.com/
https
putfile:
getfile:
time:
door:
cmd:
19990817
%s,%s,%d
Proxyserver
Software\Microsoft\Windows\CurrentVersion\Internet Settings
firefox
%s,%d
-nsunday
&hostname=
https://news.mysundayparty.com/asp/kys_allow_get.asp?name=getkys.kys
PID:%5d PATH:%s
outlook
iexplore
firefox.exe
outlook.exe
iexplore.exe
/asp/kys_allow_put.asp?type=
%s,get:%s,%d
get:%s,%d
https://news.mysundayparty.com/asp/kys_allow_get.asp?name=
The process has been unsuccessfully killed!
The process has been successfully killed!
cmd /c "echo
cmd /c "
kill
SeShutdownPrivilege
reboot false!
waiting......
reboot
process
network.proxy.http
network.proxy.http_port
NULL
prefs.js
\Mozilla\Firefox\Profiles
%s\%s
============
Local Settings\temp
File: ~.exe (same as File: nsunday.exe above)
Size: 153600
MD5: 20F8B25A9A57B07895E112DAECB1C4CC
-----------------------------------------------------------------------------------
File: dllfile.dll
Size: 27648
MD5: 15F200F08B19F26E36E7E851D7F68674
File name:dllfile.dll
http://www.virustotal.com/file-scan/report.html?id=a145a61159a4e08702fdb1c8920a78f45303297484bd3f33c83301ea9ac59df5-1288316892
Submission date:2010-10-29 01:48:12 (UTC)
18 /43 (41.9%)
Antivirus Version Last Update Result
AhnLab-V3 2010.10.29.00 2010.10.28 Win-Trojan/Wisp.27649
AntiVir 7.10.13.67 2010.10.28 HEUR/Malware
Avast 4.8.1351.0 2010.10.29 Win32:Malware-gen
Avast5 5.0.594.0 2010.10.29 Win32:Malware-gen
AVG 9.0.0.851 2010.10.28 Generic19.BYBD
BitDefender 7.2 2010.10.29 Backdoor.Generic.496992
DrWeb 5.0.2.03300 2010.10.29 BackDoor.Terapy.1
F-Secure 9.0.16160.0 2010.10.29 Backdoor.Generic.496992
GData 21 2010.10.29 Backdoor.Generic.496992
Microsoft 1.6301 2010.10.28 Trojan:Win32/Wisp.gen!A
NOD32 5573 2010.10.29 a variant of Win32/Wisp.B
nProtect 2010-10-28.01 2010.10.28 Backdoor.Generic.496992
Panda 10.0.2.7 2010.10.29 Suspicious file
PCTools 7.0.3.5 2010.10.29 Downloader.Generic
Prevx 3.0 2010.10.29 Medium Risk Malware
Sunbelt 7161 2010.10.29 Trojan.Win32.Generic!BT
Symantec 20101.2.0.161 2010.10.29 Downloader
VBA32 3.12.14.1 2010.10.28 BackDoor.Terapy.1
MD5 : 15f200f08b19f26e36e7e851d7f68674
File: dllfile.dll
MD5: 15f200f08b19f26e36e7e851d7f68674
Size: 27648
Ascii Strings: (partial)ServerDll.dll
read buffer error
cannot open the message file
ABCDEFGHIJKLMNOPQRSTUVWXYZabcdefghijklmnopqrstuvwxyz0123456789+/image/gif, image/x-xbitmap, image/jpeg, image/pjpeg, application/x-shockwave-flash, application/vnd.ms-excel, application/vnd.ms-powerpoint, application/msword, */*
Mozilla/5.0 (Windows; U; Windows NT 5.1; en-US; rv:1.9.0.7) Gecko/2009021910 Firefox/3.0.7
news.mysundayparty.com
pdnsunday.tmp
gdnsunday.tmp
pnsunday.tmp
gnsunday.tmp
POST
HTTP/1.0
http://www.yahoo.com/
https
putfile:
getfile:
time:
door:
cmd:
19990817
%s,%s,%d
Proxyserver
Network activity
Download pcap file for 65.202.221.207.pcap
65.202.221.207
 Hostname: 65.202.221.207
Hostname: 65.202.221.207ISP: Verizon Business
Organization: J R F AMERICA
Type: Corporate
Assignment: Static IP
Country: United States us flag
State/Region: Pennsylvania
City: Norristown
http://www.jrfamerica.com/
| Base | Record | Name | IP | Reverse | Route | AS | |
| news.mysundayparty.com
14 hours old
| a | 65.202.221.207
United States
| (none) | 65.192.0.0/11 | AS701
UUNET Alternet
| ||
| mysundayparty.com
14 hours old
| a | 68.178.232.100
United States
| (none) | 68.178.232.0/22 | AS26496
PAH-INC Go Daddy Software, Inc.
| ||
| ns-soa | ns09.domaincontrol.com
7 hours old
| 216.69.185.5
United States
| 216.69.185.0/24 | ||||
| ns | ns09.domaincontrol.com
7 hours old
| 216.69.185.5
United States
| |||||
| ns10.domaincontrol.com
23 hours old
(only in delegation) | 208.109.255.5
United States
| 208.109.255.0/24 | |||||
| mx | 10 | mailstore1.secureserver.net
1 hour old
| (none) | ? | |||
| 0 | smtp.secureserver.net
1 hour old
| ||||||
Domain Name: MYSUNDAYPARTY.COM
Registrar: GODADDY.COM, INC.
Whois Server: whois.godaddy.com
Referral URL: http://registrar.godaddy.com
Name Server: NS09.DOMAINCONTROL.COM
Name Server: NS10.DOMAINCONTROL.COM
Status: clientDeleteProhibited
Status: clientRenewProhibited
Status: clientTransferProhibited
Status: clientUpdateProhibited
Updated Date: 15-sep-2010
Creation Date: 15-sep-2010
Expiration Date: 15-sep-2011
The IP of news.mysundayparty.com is changing
Original was 65.202.221.207, then on Oct 30 it changed to 63.232.79.43, on Nov. 5 it is 65.202.221.207 again
news.mysundayparty.com. A 65.202.221.207
first seen 2010-10-28 23:58:14 -0000
last seen 2010-10-29 06:37:15 -0000
news.mysundayparty.com. A 63.232.79.43
first seen 2010-10-29 19:47:29 -0000
last seen 2010-10-30 13:10:27 -0000
PLEASE NOTE THE SAME DOMAIN WAS USED IN PDF POSTED
Thursday, September 16, 2010 Sep 15 CVE-2010-2883 Adobe 0-Day PDF US Government Programs to Pay Medical Expenses from rodney.cadataa@gmail.com







Doesn't disabling JavaScript in PDF mitigate this?
ReplyDeleteSample?
ReplyDeleteThis comment has been removed by a blog administrator.
ReplyDeleteDoes disabling JavaSctip prevent this exploit, or is it the authplay.dll that's being loaded and exploited regardless of the JS status?
ReplyDeleteThansk!